Last Update 10 hours ago Total Questions : 167
The Aruba Certified Network Security Associate Exam content is now fully updated, with all current exam questions added 10 hours ago. Deciding to include HPE6-A78 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our HPE6-A78 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these HPE6-A78 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Aruba Certified Network Security Associate Exam practice test comfortably within the allotted time.
Refer to the exhibit, which shows the settings on the company ' s MCs.
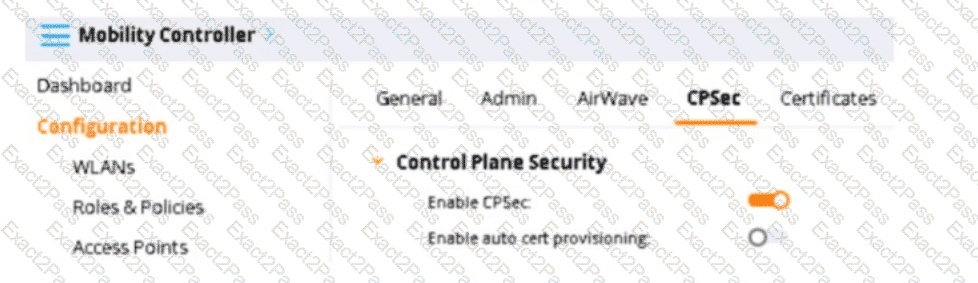
You have deployed about 100 new HPE Aruba Networking 335 APs. What is required for the APs to become managed?
The monitoring admin has asked you to set up an AOS-CX switch to meet these criteria:
Send logs to a SIEM Syslog server at 10.4.13.15 at the standard TCP port (514)
Send a log for all events at the " warning " level or above; do not send logs with a lower level than " warning " The switch did not have any " logging " configuration on it. You then entered this command: AOS-CX(config)# logging 10.4.13.15 tcp vrf default What should you do to finish configuring to the requirements?
Your company policies require you to encrypt logs between network infrastructure devices and Syslog servers. What should you do to meet these requirements on an ArubaOS-CX switch?
A client has accessed an HTTPS server at myhost1.example.com using Chrome. The server sends a certificate that includes these properties:
Subject name: myhost.example.com
SAN: DNS: myhost.example.com; DNS: myhost1.example.com
Extended Key Usage (EKU): Server authentication
Issuer: MyCA_Signing The server also sends an intermediate CA certificate for MyCA_Signing, which is signed by MyCA. The client’s Trusted CA Certificate list does not include the MyCA or MyCA_Signing certificates. Which factor or factors prevent the client from trusting the certificate?
Refer to the exhibit, which shows the current network topology.
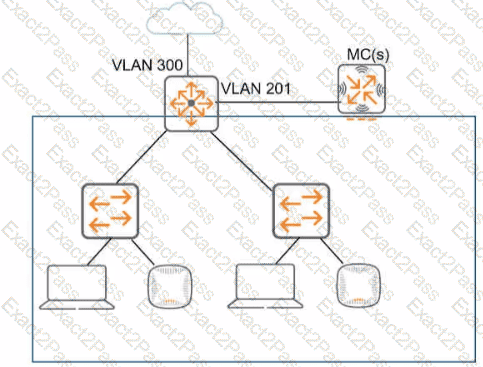
You are deploying a new wireless solution with an Aruba Mobility Master (MM). Aruba Mobility Controllers (MCs). and campus APs (CAPs). The solution will Include a WLAN that uses Tunnel for the forwarding mode and Implements WPA3-Enterprise security
What is a guideline for setting up the vlan for wireless devices connected to the WLAN?
What are the roles of 802.1X authenticators and authentication servers?
What is a benefit of deploying Aruba ClearPass Device insight?
How does the AOS firewall determine which rules to apply to a specific client ' s traffic?
What is one of the policies that a company should define for digital forensics?
You have been instructed to look in the ArubaOS Security Dashboard ' s client list. Your goal is to find clients that belong to the company and have connected to devices that might belong to hackers.
Which client fits this description?

