Last Update 51 minutes ago Total Questions : 93
The Netskope Certified Cloud Security Integrator (NCCSI) content is now fully updated, with all current exam questions added 51 minutes ago. Deciding to include NSK200 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our NSK200 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these NSK200 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Netskope Certified Cloud Security Integrator (NCCSI) practice test comfortably within the allotted time.
Your customer has some managed Windows-based endpoints where they cannot add any clients or agents. For their users to have secure access to their SaaS application, you suggest that the customer use Netskope ' s Explicit Proxy.
Which two configurations are supported for this use case? (Choose two.)
Your company is using on-premises QRadar as a SIEM solution. They are replacing it with Rapid7 in the cloud. The legacy on-premises QRadar will eventually be decommissioned. Your IT department does not want to use the same token that QRadar uses.
You are deploying a Netskope client in your corporate office network. You are aware of firewall or proxy rules that need to be modified to allow traffic.
Which two statements are true in this scenario? (Choose two.)
Your IT organization is migrating its user directory services from Microsoft Active Directory to a cloud-based Identity Provider (IdP) solution, Azure AD. You are asked to adapt the Netskope user provisioning process to work with this new cloud-based IdP.
An engineering firm is using Netskope DLP to identify and block sensitive documents, including schematics and drawings. Lately, they have identified that when these documents are blocked, certain employees may be taking screenshots and uploading them. They want to block any screenshots from being uploaded.
Which feature would you use to satisfy this requirement?
Your small company of 10 people wants to deploy the Netskope client to all company users without requiring users to be imported using Active Directory, LDAP, or an IdP.
Review the exhibit.
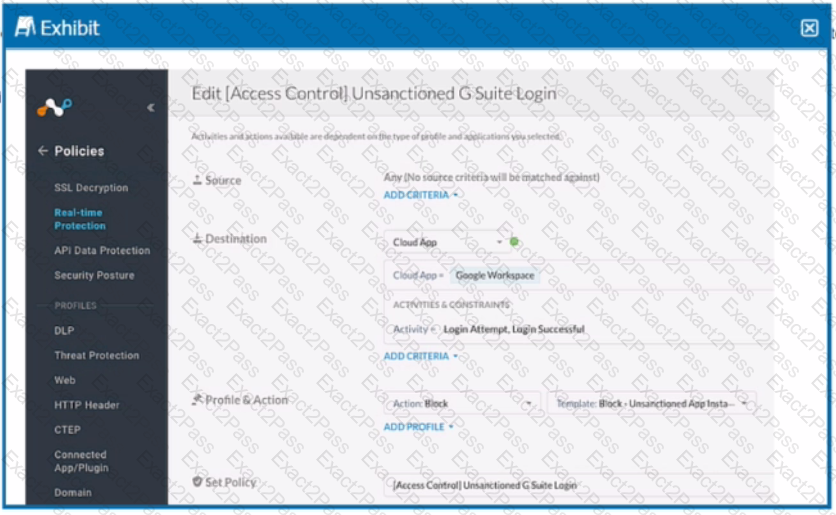
Your company uses Google as the corporate collaboration suite; however, corporate policy restricts the use of personal Google services. The exhibit provides a partially completed policy to ensure that users cannot log into their personal account.
What should be added to achieve the desired outcome in this scenario?
After deploying the Netskope client to a number of devices, users report that the Client status indicates " Admin Disabled " . User and gateway information is displayed correctly in the client configuration dialog
Why are clients installing in an " Admin Disabled " state in this scenario?
You are testing policies using the DLP predefined identifier " Card Numbers (Major Networks; all). " No DLP policy hits are observed.
You want to secure Microsoft Exchange and Gmail SMTP traffic for DLP using Netskope. Which statement is true about this scenario when using the Netskope client?

