Last Update 23 hours ago Total Questions : 93
The Netskope Certified Cloud Security Integrator (NCCSI) content is now fully updated, with all current exam questions added 23 hours ago. Deciding to include NSK200 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our NSK200 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these NSK200 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Netskope Certified Cloud Security Integrator (NCCSI) practice test comfortably within the allotted time.
Review the exhibit.
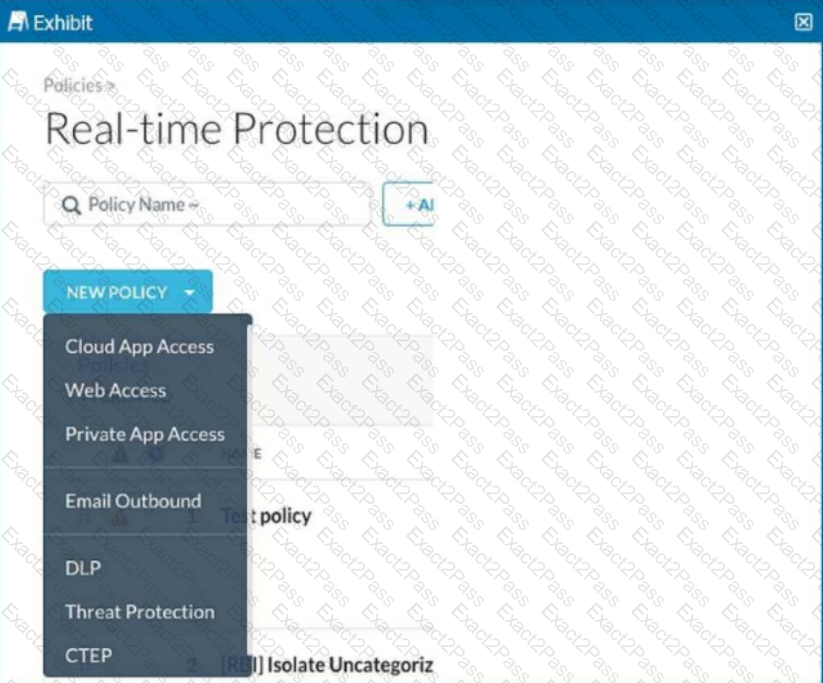
You are asked to create a new Real-time Protection policy to scan SMTP emails using data loss prevention (DLP) for personal health information (PHI). The scope is limited to only emails being sent from Microsoft Exchange Online to outside recipients.
A city uses many types of forms, including permit applications. These forms contain personal and financial information of citizens. Remote employees download these forms and work directly with the citizens to complete them. The city wants to be able to identify and monitor the specific forms and block the employees from downloading completed forms.
Which feature would you use to accomplish this task?
Review the exhibit.
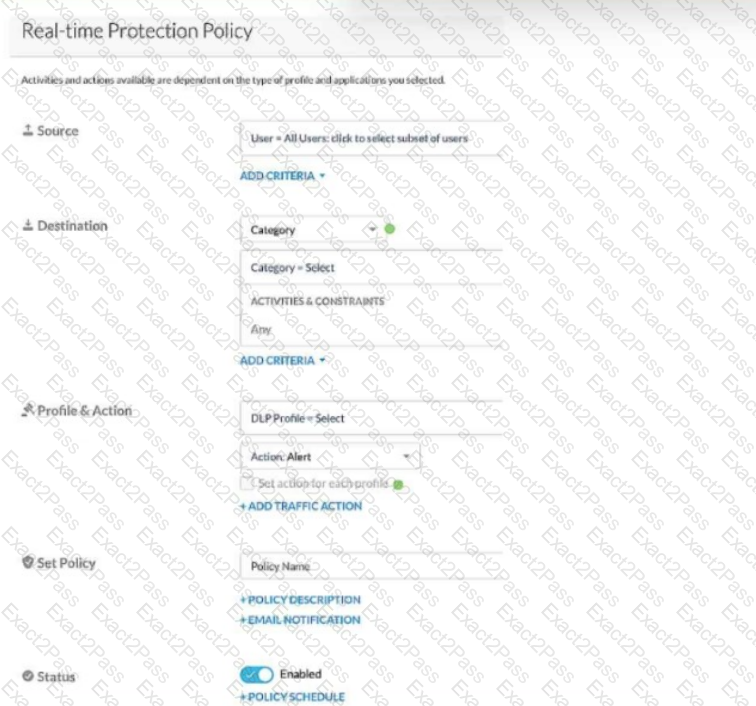
Given the information shown below:
- for PCI data uploads, you want to provide no notification,
- for PHI data uploads, you want to allow users to proceed by clicking OK,
- for GDPR data uploads, you want to provide block notification,
- if none of the above matches, you want to provide no notification.
You want to reduce the number of policies by combining multiple DLP profiles Into one policy.
Referring to the exhibit, which two statements are true? (Choose two.)
Review the exhibit.
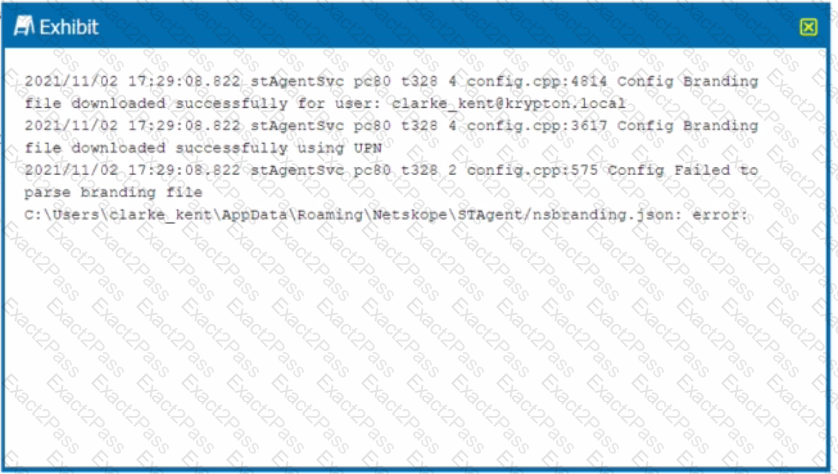
You receive a service request from a user who indicates that their Netskope client is in a disabled state. The exhibit shows an excerpt (rom the affected client nsdebuglog.log.
What is the problem in this scenario?
Which statement describes a requirement for deploying a Netskope Private Application (NPA) Publisher?
You want to prevent a document stored in Google Drive from being shared externally with a public link. What would you configure in Netskope to satisfy this requirement?
You are an administrator writing Netskope Real-time Protection policies and must determine proper policy ordering.
Which two statements are true in this scenario? (Choose two.)

