Last Update 4 hours ago Total Questions : 221
The CyberArk CDE Recertification content is now fully updated, with all current exam questions added 4 hours ago. Deciding to include PAM-CDE-RECERT practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our PAM-CDE-RECERT exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these PAM-CDE-RECERT sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CyberArk CDE Recertification practice test comfortably within the allotted time.
Assuming a safe has been configured to be accessible during certain hours of the day, a Vault Admin may still access that safe outside of those hours.
Can the 'Connect' button be used to initiate an SSH connection, as root, to a Unix system when SSH access for root is denied?
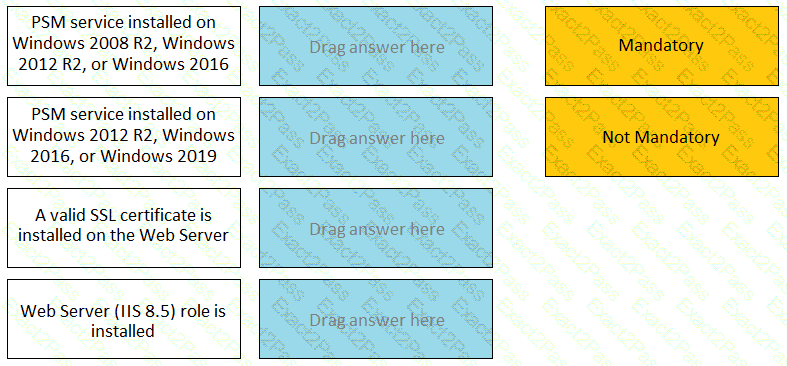
For each listed prerequisite, identify if it is mandatory or not mandatory to run the PSM Health Check.
A user requested access to view a password secured by dual-control and is unsure who to contact to expedite the approval process. The Vault Admin has been asked to look at the account and identify who can approve their request.
What is the correct location to identify users or groups who can approve?
Which PTA sensors are required to detect suspected credential theft?
Which is the primary purpose of exclusive accounts?
Which parameter controls how often the CPM looks for accounts that need to be changed from recently completed Dual control requests.
Which built-in report from the reports page in PVWA displays the number of days until a password is due to expire?
Which Master Policy Setting must be active in order to have an account checked-out by one user for a pre-determined amount of time?
Due to network activity, ACME Corp’s PrivateArk Server became active on the OR Vault while the Primary Vault was also running normally. All the components continued to point to the Primary Vault.
Which steps should you perform to restore DR replication to normal?

