Last Update 21 hours ago Total Questions : 210
The Microsoft Security Compliance and Identity Fundamentals content is now fully updated, with all current exam questions added 21 hours ago. Deciding to include SC-900 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our SC-900 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these SC-900 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Microsoft Security Compliance and Identity Fundamentals practice test comfortably within the allotted time.
Which three statements accurately describe the guiding principles of Zero Trust? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
What are two capabilities of Microsoft Defender for Endpoint? Each correct selection presents a complete solution.
NOTE: Each correct selection is worth one point.
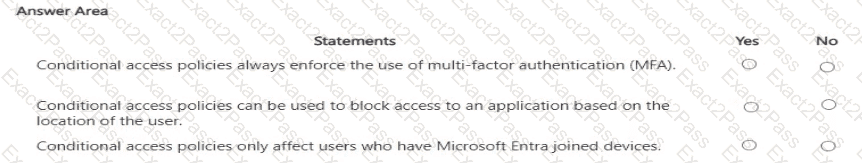
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
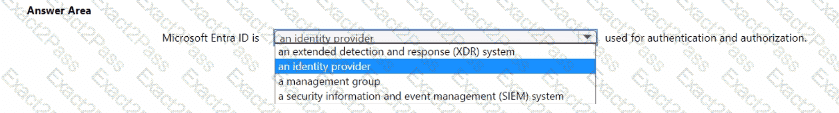
Select the answer that correctly completes the sentence.
Which Microsoft Purview data classification type supports the use of regular expressions?
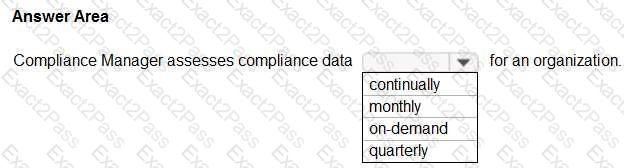
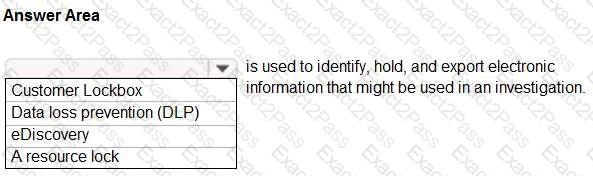
Select the answer that correctly completes the sentence.
What do you use to provide real-time integration between Azure Sentinel and another security source?
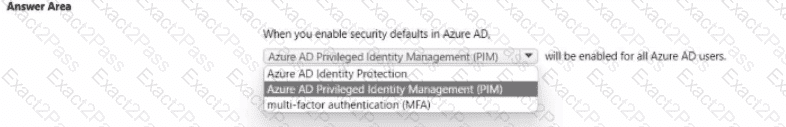
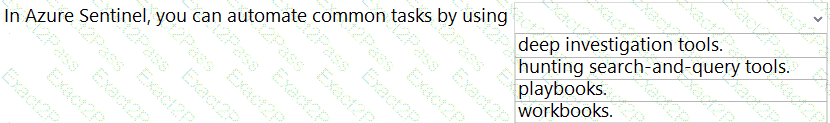
Select the answer that correctly completes the sentence.
Select the answer that correctly completes the sentence.
Select the answer that correctly completes the sentence.