Last Update 22 hours ago Total Questions : 99
The Splunk Certified Cybersecurity Defense Analyst content is now fully updated, with all current exam questions added 22 hours ago. Deciding to include SPLK-5001 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our SPLK-5001 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these SPLK-5001 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Splunk Certified Cybersecurity Defense Analyst practice test comfortably within the allotted time.
Which of the following is the primary benefit of using the CIM in Splunk?
Which of the following compliance frameworks was specifically created to measure the level of cybersecurity maturity within an organization?
How are Notable Events configured in Splunk Enterprise Security?
After discovering some events that were missed in an initial investigation, an analyst determines this is because some events have an empty src field. Instead, the required data is often captured in another field called machine_name.
What SPL could they use to find all relevant events across either field until the field extraction is fixed?
Which of the following is not a component of the Splunk Security Content library (ESCU, SSE)?
Which Enterprise Security framework provides a mechanism for running preconfigured actions within the Splunk platform or integrating with external applications?
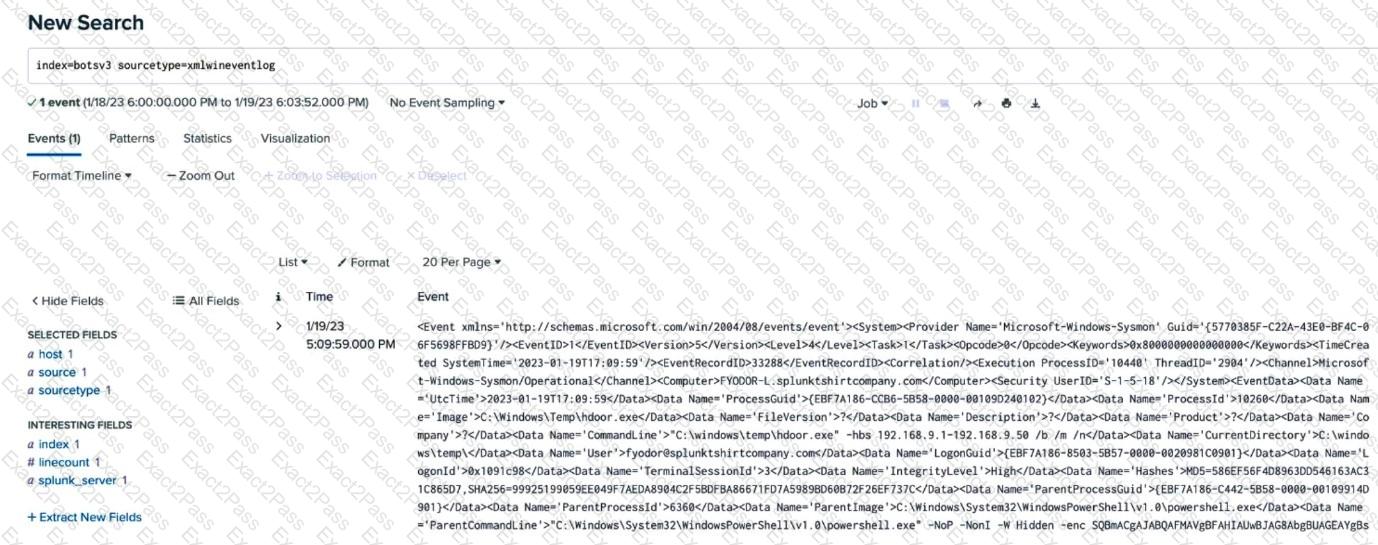
An analyst is building a search to examine Windows XML Event Logs, but the initial search is not returning any extracted fields. Based on the above image, what is themost likelycause?

