Last Update 3 hours ago Total Questions : 175
The Implementing Secure Solutions with Virtual Private Networks (SVPN) content is now fully updated, with all current exam questions added 3 hours ago. Deciding to include 300-730 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 300-730 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 300-730 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Implementing Secure Solutions with Virtual Private Networks (SVPN) practice test comfortably within the allotted time.
Which parameter is initially used to elect the primary key server from a group of key servers?
An engineer is requesting an SSL certificate for a VPN load-balancing cluster in which two Cisco ASAs provide clientless SSLVPN access. The FQDN that users will enter to access the clientless VPN is asa.example.com, and users will be redirected to either asa1.example.com or asa2.example.com. The cluster FQDN and individual Cisco ASAs FQDNs resolve to IP addresses 192.168.0.1, 192.168.0.2, and 192.168.0.3 respectively. The issued certificate must be able to be used to validate the identity of either ASA in the cluster without returning any certificate validation errors. Which fields must be included in the certificate to meet these requirements?
Which remote access VPN technology requires the use of the IPsec-proposal configuration option?
A network engineer has almost finished setting up a clientless VPN that allows remote users to access internal HTTP servers. Users must enter their username and password twice: once on the clientless VPN web portal and again to log in to internal HTTP servers. The Cisco ASA and the HTTP servers use the same Active Directory server to authenticate users. Which next step must be taken to allow users to enter their password only once?
Refer to the exhibit.
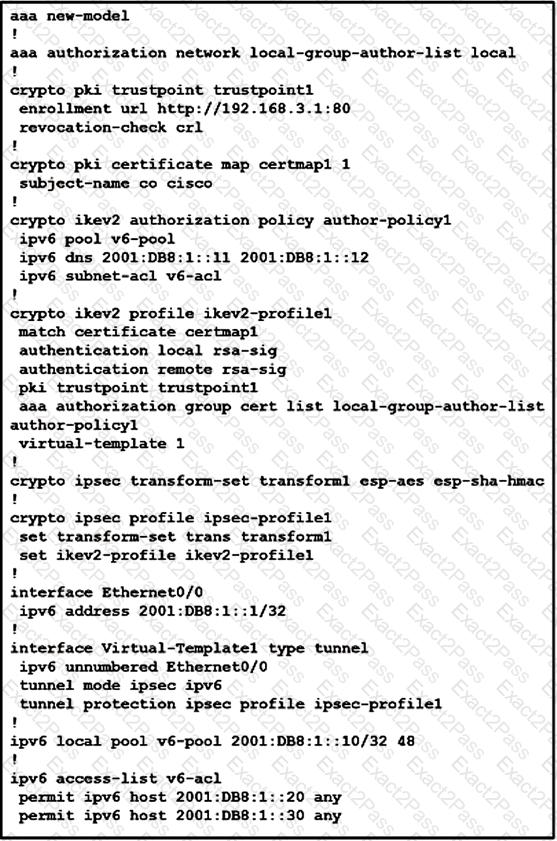
What is configured as a result of this command set?
Which statement about GETVPN is true?
Which method dynamically installs the network routes for remote tunnel endpoints?
Refer to the exhibit.

A customer cannot establish an IKEv2 site-to-site VPN tunnel between two Cisco ASA devices. Based on the syslog message, which action brings up the VPN tunnel?
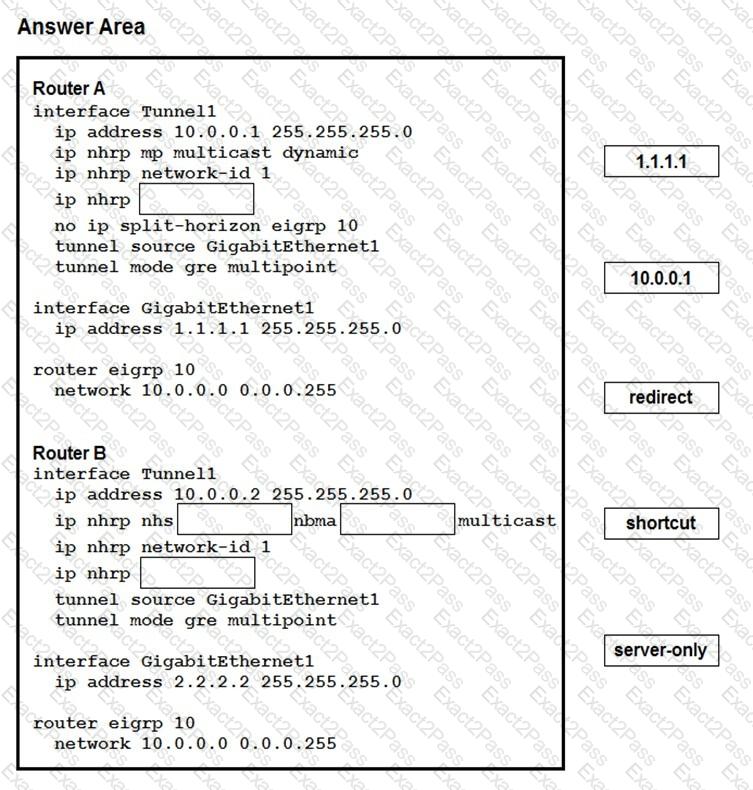
Drag and drop the correct commands from the night onto the blanks within the code on the left to implement a design that allow for dynamic spoke-to-spoke communication. Not all comments are used.
Which two changes must be made in order to migrate from DMVPN Phase 2 to Phase 3 when EIGRP is configured? (Choose two.)

