Last Update 13 hours ago Total Questions : 61
The Designing and Implementing Secure Cloud Access for Users and Endpoints (SCAZT) content is now fully updated, with all current exam questions added 13 hours ago. Deciding to include 300-740 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 300-740 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 300-740 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Designing and Implementing Secure Cloud Access for Users and Endpoints (SCAZT) practice test comfortably within the allotted time.
According to Cisco Security Reference Architecture, which solution provides threat intelligence and malware analytics?
An administrator must deploy an endpoint posture policy for all users. The organization wants to have all endpoints checked against antimalware definitions and operating system updates and ensure that the correct Secure Client modules are installed properly. How must the administrator meet the requirements?
An administrator received an incident report indicating suspicious activity of a user using a corporate device. The manager requested that the credentials of user user1@cisco.com be reset and synced via the Active Directory. Removing the account should be avoided and used for further investigation on data leak. Which configuration must the administrator apply on the Duo Admin Panel?
An engineer configures trusted endpoints with Active Directory with Device Health to determine if an endpoint complies with the policy posture. After a week, an alert is received by one user, reporting problems accessing an application. When the engineer verifies the authentication report, this error is found:
" Endpoint is not trusted because Cisco Secure Endpoint check failed, Check user ' s endpoint in Cisco Secure Endpoint. "
Which action must the engineer take to permit access to the application again?
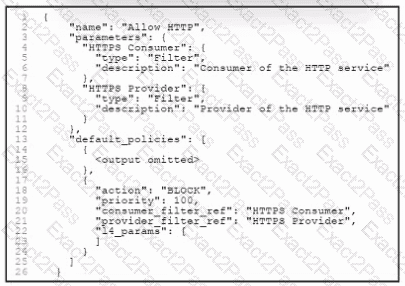
Refer to the exhibit. An engineer must create a segmentation policy in Cisco Secure Workload to block HTTP traffic. The indicated configuration was applied; however, HTTP traffic is still allowed. What should be done to meet the requirement?
How does Cisco XDR perform threat prioritization by using its visibility across multiple platforms?
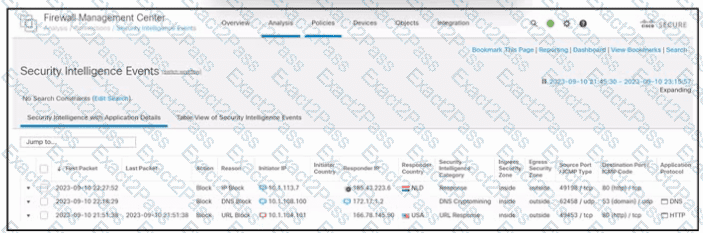
Refer to the exhibit. An engineer is analyzing a Cisco Secure Firewall Management Center report. Which activity does the output verify?
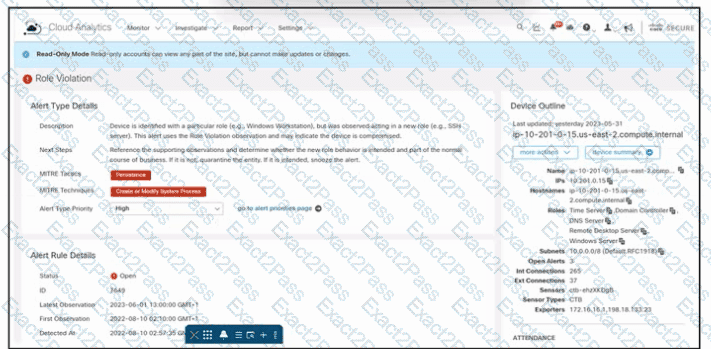
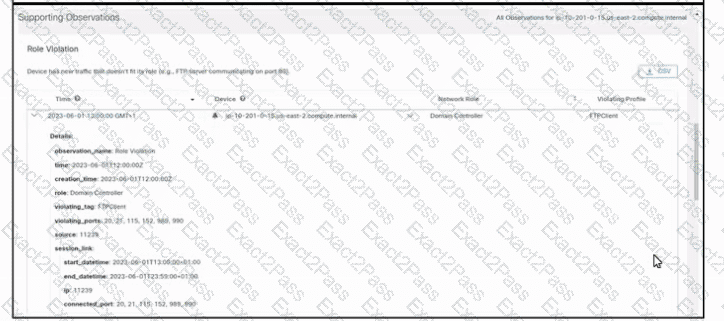
Refer to the exhibit. An engineer is troubleshooting an incident by using Cisco Secure Cloud Analytics. What is the cause of the issue?

