Last Update 12 hours ago Total Questions : 61
The Designing and Implementing Secure Cloud Access for Users and Endpoints (SCAZT) content is now fully updated, with all current exam questions added 12 hours ago. Deciding to include 300-740 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 300-740 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 300-740 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Designing and Implementing Secure Cloud Access for Users and Endpoints (SCAZT) practice test comfortably within the allotted time.
What is associated with implementing Cisco zero-trust architecture?
Which types of algorithm does a web application firewall use for zero-day DDoS protection?
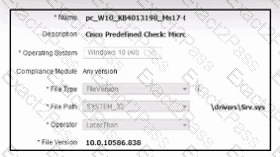
Refer to the exhibit. A security engineer must configure a posture policy in Cisco ISE to ensure that employee laptops have a critical patch for WannaCry installed before they can access the network. Which posture condition must the engineer configure?
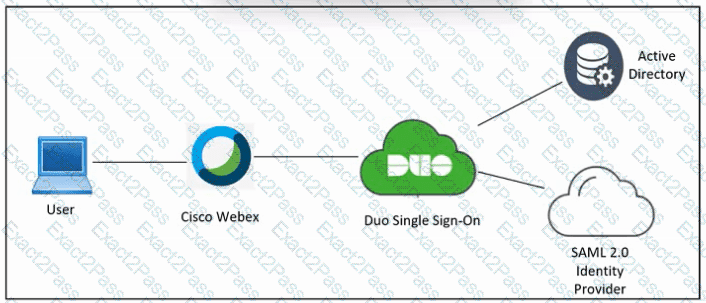
Refer to the exhibit. An engineer must configure Duo SSO for Cisco Webex and add the Webex application to the Duo Access Gateway. Which two actions must be taken in Duo? (Choose two.)
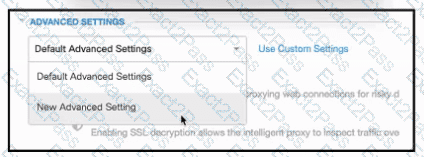
Refer to the exhibit. An engineer must configure a global allow list in Cisco Umbrella for the cisco.com domain. All other domains must be blocked. After creating a new policy and adding the cisco.com domain, the engineer attempts to access a site outside of cisco.com and is successful. Which additional Security Settings action must be taken to meet the requirement?
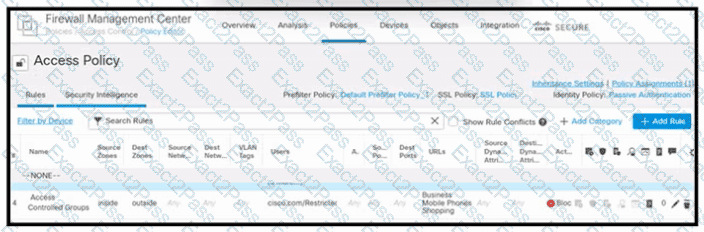
Refer to the exhibit. An engineer must create a policy in Cisco Secure Firewall Management Center to prevent restricted users from being able to browse any business or mobile phone shopping websites. The indicated policy was applied; however, the restricted users still can browse on the mobile phone shopping websites during business hours. What should be done to meet the requirement?
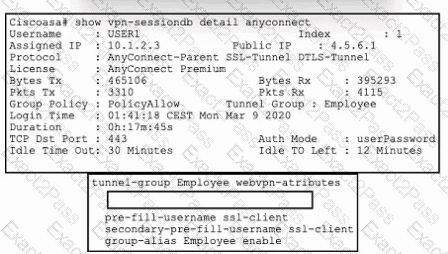
Refer to the exhibit. An engineer must implement a remote access VPN solution that provides user and device verification. The company uses Active Directory for user authentication and ID certificates for device identity. Users are currently able to connect using only a valid username and password, even if their computer is missing the required certificate.
Which command from the Cisco ASA tunnel-group completes the requirement of verifying device identity in addition to user identity?

