Last Update 22 hours ago Total Questions : 704
The Computer Hacking Forensic Investigator (CHFI-v10) content is now fully updated, with all current exam questions added 22 hours ago. Deciding to include 312-49v10 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-49v10 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-49v10 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Computer Hacking Forensic Investigator (CHFI-v10) practice test comfortably within the allotted time.
To which phase of the computer forensics investigation process does " planning and budgeting of a forensics lab " belong?
The information security manager at a national legal firm has received several alerts from the intrusion detection system that a known attack signature was detected against the organization ' s file server. What should the information security manager do first?
A call detail record (CDR) provides metadata about calls made over a phone service. From the following data fields, which one Is not contained in a CDR.
During an Investigation. Noel found a SIM card from the suspect ' s mobile. The ICCID on the card is
8944245252001451548.
What does the first four digits (89 and 44) In the ICCID represent?
Web browsers can store relevant information from user activities. Forensic investigators may retrieve files, lists, access history, cookies, among other digital footprints. Which tool can contribute to this task?
You are a forensic investigator who is analyzing a hard drive that was recently collected as evidence. You have been unsuccessful at locating any meaningful evidence within the file system and suspect a drive wiping utility may have been used. You have reviewed the keys within the software hive of the Windows registry and did not find any drive wiping utilities. How can you verify that drive wiping software was used on the hard drive?
Which of the following attacks refers to unintentional download of malicious software via the Internet? Here, an attacker exploits flaws in browser software to install malware merely by the user visiting the malicious website.
What happens lo the header of the file once It Is deleted from the Windows OS file systems?
Jacob, a cybercrime investigator, joined a forensics team to participate in a criminal case involving digital evidence. After the investigator collected all the evidence and presents it to the court, the judge dropped the case and the defense attorney pressed charges against Jacob and the rest of the forensics team for unlawful search and seizure. What forensics privacy issue was not addressed prior to collecting the evidence?
During a forensic investigation, a large number of files were collected. The investigator needs to evaluate ownership and accountability of those files. Therefore, he begins to Identify attributes such as " author name, " " organization name. " " network name, " or any additional supporting data that is meant for the owner ' s Identification purpose. Which term describes these attributes?
Sally accessed the computer system that holds trade secrets of the company where she Is employed. She knows she accessed It without authorization and all access (authorized and unauthorized) to this computer Is monitored.To cover her tracks. Sally deleted the log entries on this computer. What among the following best describes her action?
A forensic analyst has been tasked with investigating unusual network activity Inside a retail company ' s network. Employees complain of not being able to access services, frequent rebooting, and anomalies In log files. The Investigator requested log files from the IT administrator and after carefully reviewing them, he finds the following log entry:
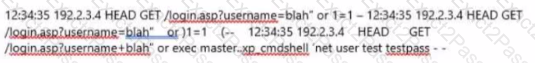
What type of attack was performed on the companies ' web application?
A computer forensics Investigator or forensic analyst Is a specially trained professional who works with law enforcement as well as private businesses to retrieve Information from computers and other types of data storage devices. For this, the analyst should have an excellent working knowledge of all aspects of the computer. Which of the following is not a duty of the analyst during a criminal investigation?
What command-line tool enables forensic Investigator to establish communication between an Android device and a forensic workstation in order to perform data acquisition from the device?
Identify the location of Recycle Bin on a Windows 7 machine that uses NTFS file system to store and retrieve files on the hard disk.

