Last Update 20 hours ago Total Questions : 704
The Computer Hacking Forensic Investigator (CHFI-v10) content is now fully updated, with all current exam questions added 20 hours ago. Deciding to include 312-49v10 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-49v10 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-49v10 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Computer Hacking Forensic Investigator (CHFI-v10) practice test comfortably within the allotted time.
Cylie is investigating a network breach at a state organization in Florida. She discovers that the intruders were able to gain access into the company firewalls by overloading them with IP packets. Cylie then discovers through her investigation that the intruders hacked into the company phone system and used the hard drives on their PBX system to store shared music files. What would this attack on the company PBX system be called?
Which of the following is NOT an anti-forensics technique?
Which of the following statements is TRUE with respect to the Registry settings in the user start-up folder HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce\.
Self-Monitoring, Analysis, and Reporting Technology (SMART) is built into the hard drives to monitor and report system activity. Which of the following is included in the report generated by SMART?
Which of the following files contains the traces of the applications installed, run, or uninstalled from a system?
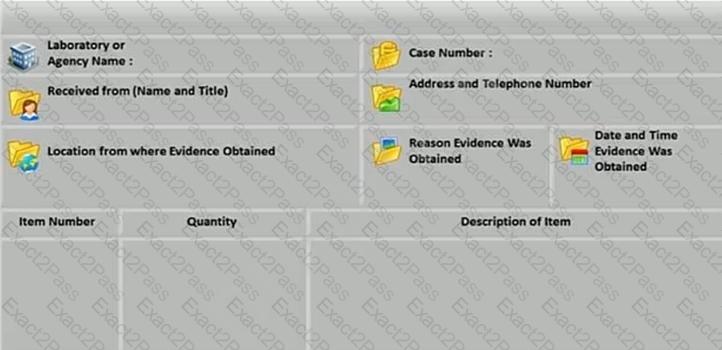
What document does the screenshot represent?
Which of the following Perl scripts will help an investigator to access the executable image of a process?
Investigators can use the Type Allocation Code (TAC) to find the model and origin of a mobile device. Where is TAC located in mobile devices?
Which of the following tool is used to locate IP addresses?
Which of these Windows utility help you to repair logical file system errors?
The MAC attributes are timestamps that refer to a time at which the file was last modified or last accessed or originally created. Which of the following file systems store MAC attributes in Coordinated Universal Time (UTC) format?
Gary, a computer technician, is facing allegations of abusing children online by befriending them and sending them illicit adult images from his office computer. What type of investigation does this case require?
MAC filtering is a security access control methodology, where a ___________ is assigned to each network card to determine access to the network.
Rusty, a computer forensics apprentice, uses the command nbtstat –c while analyzing the network information in a suspect system. What information is he looking for?
Email archiving is a systematic approach to save and protect the data contained in emails so that it can be accessed fast at a later date. There are two main archive types, namely Local Archive and Server Storage Archive. Which of the following statements is correct while dealing with local archives?

