Last Update 14 hours ago Total Questions : 614
The Certified Ethical Hacker Exam content is now fully updated, with all current exam questions added 14 hours ago. Deciding to include 312-50 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-50 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-50 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Ethical Hacker Exam practice test comfortably within the allotted time.
Which of the following can take an arbitrary length of input and produce a message digest output of 160 bit?
Craig received a report of all the computers on the network that showed all the missing patches and weak passwords. What type of software generated this report?
Which statement is TRUE regarding network firewalls preventing Web Application attacks?
Defining rules, collaborating human workforce, creating a backup plan, and testing the plans are within what phase of the Incident Handling Process?
Which of the following is a hardware requirement that either an IDS/IPS system or a proxy server must have in order to properly function?
Employees in a company are no longer able to access Internet web sites on their computers. The network administrator is able to successfully ping IP address of web servers on the Internet and is able to open web sites by using an IP address in place of the URL. The administrator runs the nslookup command for www.eccouncil.org and receives an error message stating there is no response from the server. What should the administrator do next?
A security policy will be more accepted by employees if it is consistent and has the support of
The Heartbleed bug was discovered in 2014 and is widely referred to under MITRE’s Common Vulnerabilities and Exposures (CVE) as CVE-2014-0160. This bug affects the OpenSSL implementation of the transport layer security (TLS) protocols defined in RFC6520.
What type of key does this bug leave exposed to the Internet making exploitation of any compromised system very easy?
As an Ethical Hacker you are capturing traffic from your customer network with Wireshark and you need to find and verify just SMTP traffic. What command in Wireshark will help you to find this kind of traffic?
Emil uses nmap to scan two hosts using this command.
nmap -sS -T4 -O 192.168.99.1 192.168.99.7
He receives this output:
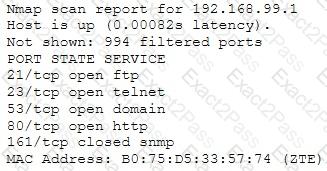
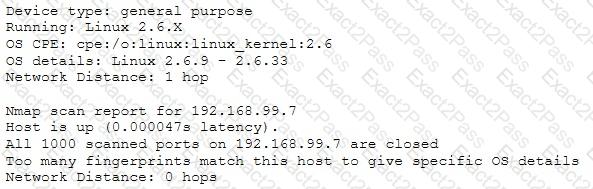
What is his conclusion?

