Last Update 14 hours ago Total Questions : 614
The Certified Ethical Hacker Exam content is now fully updated, with all current exam questions added 14 hours ago. Deciding to include 312-50 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-50 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-50 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Ethical Hacker Exam practice test comfortably within the allotted time.
Nathan is testing some of his network devices. Nathan is using Macof to try and flood the ARP cache of these switches.
If these switches ' ARP cache is successfully flooded, what will be the result?
Which of the following statements about a zone transfer is correct? (Choose three.)
What does a type 3 code 13 represent? (Choose two.)
Which of the following is a restriction being enforced in “white box testing?”
Which of the following command line switch would you use for OS detection in Nmap?
Your team has won a contract to infiltrate an organization. The company wants to have the attack be as realistic as possible; therefore, they did not provide any information besides the company name.
What should be the first step in security testing the client?
Eve stole a file named secret.txt, transferred it to her computer and she just entered these commands:
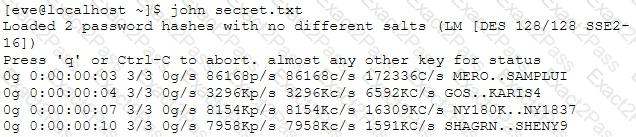
What is she trying to achieve?
Which of the following tools are used for enumeration? (Choose three.)
In which phase of the ethical hacking process can Google hacking be employed? This is a technique that involves manipulating a search string with specific operators to search for vulnerabilities.
Example:
allintitle: root passwd
It is a widely used standard for message logging. It permits separation of the software that generates messages, the system that stores them, and the software that reports and analyzes th em. This protocol is specifically designed for transporting event messages. Which of the following is being described?

