Last Update 16 hours ago Total Questions : 614
The Certified Ethical Hacker Exam content is now fully updated, with all current exam questions added 16 hours ago. Deciding to include 312-50 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-50 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-50 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Ethical Hacker Exam practice test comfortably within the allotted time.
Windows file servers commonly hold sensitive files, databases, passwords and more. Which of the following choices would be a common vulnerability that usually exposes them?
Which of the following is an example of an asymmetric encryption implementation?
An attacker uses a communication channel within an operating system that is neither designed nor intended to transfer information. What is the name of the communications channel?
A company has hired a security administrator to maintain and administer Linux and Windows-based systems. Written in the nightly report file is the following:
Firewall log files are at the expected value of 4 MB. The current time is 12am. Exactly two hours later the size has decreased considerably. Another hour goes by and the log files have shrunk in size again.
Which of the following actions should the security administrator take?
What is the name of the international standard that establishes a baseline level of confidence in the security functionality of IT products by providing a set of requirements for evaluation?
Which of the following is a symmetric cryptographic standard?
Which of the following techniques does a vulnerability scanner use in order to detect a vulnerability on a target service?
A company firewall engineer has configured a new DMZ to allow public systems to be located away from the internal network. The engineer has three security zones set:
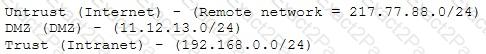
The engineer wants to configure remote desktop access from a fixed IP on the remote network to a remote desktop server in the DMZ. Which rule would best fit this requirement?
Which of the following types of firewall inspects only header information in network traffic?
Which type of scan is used on the eye to measure the layer of blood vessels?

