Last Update 12 hours ago Total Questions : 232
The EC-Council Certified Security Analyst (ECSA) content is now fully updated, with all current exam questions added 12 hours ago. Deciding to include 412-79 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 412-79 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 412-79 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any EC-Council Certified Security Analyst (ECSA) practice test comfortably within the allotted time.
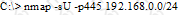
What is the following command trying to accomplish?
After passing her CEH exam, Carol wants to ensure that her network is completely secure. She implements a DMZ, statefull firewall, NAT, IPSEC, and a packet filtering firewall. Since all security measures were taken, none of the hosts on her network can reach the Internet. Why is that?
Your company ' s network just finished going through a SAS 70 audit. This audit reported that overall, your network is secure, but there are some areas that needs improvement. The major area was SNMP security. The audit company recommended turning off SNMP, but that is not an option since you have so many remote nodes to keep track of. What step could you take to help secure SNMP on your network?
To preserve digital evidence, an investigator should ____________________
A law enforcement officer may only search for and seize criminal evidence with _____________, which are facts or circumstances that would lead a reasonable person to believe a crime has been committed or is about to be committed, evidence of the specific crime exists and the evidence of the specific crime exists at the place to be searcheD.
Diskcopy is:
This organization maintains a database of hash signatures for known software:
Profiling is a forensics technique for analyzing evidence with the goal of identifying the perpetrator from their various activity. After a computer has been compromised by a hacker, which of the following would be most important in forming a profile of the incident?
When investigating a Windows System, it is important to view the contents of the page or swap file because:
The use of warning banners helps a company avoid litigation by overcoming an employees assumed
____________ When connecting to the company‟s intranet, network or Virtual Private Network(VPN) and will allow the company‟s investigators to monitor, search and retrieve information stored within the network.

