Last Update 12 hours ago Total Questions : 232
The EC-Council Certified Security Analyst (ECSA) content is now fully updated, with all current exam questions added 12 hours ago. Deciding to include 412-79 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 412-79 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 412-79 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any EC-Council Certified Security Analyst (ECSA) practice test comfortably within the allotted time.
The ____________________ refers to handing over the results of private investigations to the authorities because of indications of criminal activity.
If you come across a sheepdip machine at your client site, what would you infer?
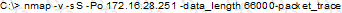
What will the following command accomplish?
Jonathan is a network administrator who is currently testing the internal security of his network. He is attempting to hijack a session, using Ettercap, of a user connected to his Web server. Why will Jonathan not succeed?
At what layer of the OSI model do routers function on?
Jim performed a vulnerability analysis on his network and found no potential problems. He runs another utility that executes exploits against his system to verify the results of the vulnerability test. The second utility executes five known exploits against his network in which the vulnerability analysis said were not exploitable. What kind of results did Jim receive from his vulnerability analysis?
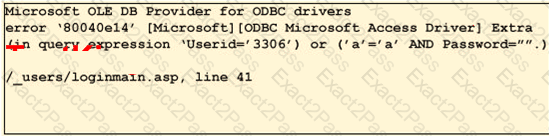
To test your website for vulnerabilities, you type in a quotation mark (? for the username field. After you click Ok, you receive the following error message window:
What can you infer from this error window?
Exhibit:
If an attacker ' s computer sends an IPID of 31400 to a zombie computer on an open port in IDLE scanning, what will be the response?
You have compromised a lower-level administrator account on an Active Directory network of a small company in Dallas, Texas. You discover Domain Controllers through enumeration. You connect to one of the Domain Controllers on port 389 using ldp.exe. What are you trying to accomplish here?
Frank is working on a vulnerability assessment for a company on the West coast. The company hired Frank to assess its network security through scanning, pen tests, and vulnerability assessments. After discovering numerous known vulnerabilities detected by a temporary IDS he set up, he notices a number of items that show up as unknown but questionable in the logs. He looks up the behavior on the Internet, but cannot find anything related. What organization should Frank submit the log to find out if it is a new vulnerability or not?

