Last Update 12 hours ago Total Questions : 232
The EC-Council Certified Security Analyst (ECSA) content is now fully updated, with all current exam questions added 12 hours ago. Deciding to include 412-79 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 412-79 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 412-79 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any EC-Council Certified Security Analyst (ECSA) practice test comfortably within the allotted time.
What is kept in the following directory? HKLM\SECURITY\Policy\Secrets
Harold is a security analyst who has just run the rdisk /s command to grab the backup SAM file on a computer. Where should Harold navigate on the computer to find the file?
John is using Firewalk to test the security of his Cisco PIX firewall. He is also utilizing a sniffer located on a subnet that resides deep inside his network. After analyzing the sniffer log files, he does not see any of the traffic produced by Firewalk. Why is that?
What will the following command produce on a website login page?
SELECT email, passwd, login_id, full_name
FROM members
WHERE email = ' someone@somehwere.com ' ; DROP TABLE members; -- '
You are the network administrator for a small bank in Dallas, Texas. To ensure network security, you enact a security policy that requires all users to have 14 character passwords. After giving your users 2 weeks notice, you change the Group Policy to force 14 character passwords. A week later you dump the SAM database from the standalone server and run a password-cracking tool against it. Over 99% of the passwords are broken within an hour. Why were these passwords cracked so quickly?
At what layer of the OSI model do routers function on?
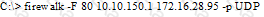
What is the target host IP in the following command?
In Linux, what is the smallest possible shellcode?
Harold is a security analyst who has just run the rdisk /s command to grab the backup SAM file on a computer. Where should Harold navigate on the computer to find the file?
Michael works for Kimball Construction Company as senior security analyst. As part of yearly security audit, Michael scans his network for vulnerabilities. Using Nmap, Michael conducts XMAS scan and most of the ports scanned do not give a response. In what state are these ports?

