Last Update 17 hours ago Total Questions : 878
The Certified Ethical Hacker (CEH) content is now fully updated, with all current exam questions added 17 hours ago. Deciding to include CEH-001 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CEH-001 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CEH-001 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Ethical Hacker (CEH) practice test comfortably within the allotted time.
What is the broadcast address for the subnet 190.86.168.0/22?
A covert channel is a channel that
Which type of password cracking technique works like dictionary attack but adds some numbers and symbols to the words from the dictionary and tries to crack the password?
Exhibit
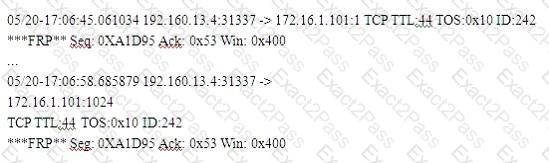
(Note: the student is being tested on concepts learnt during passive OS fingerprinting, basic TCP/IP connection concepts and the ability to read packet signatures from a sniff dump.)
Snort has been used to capture packets on the network. On studying the packets, the penetration tester finds it to be abnormal. If you were the penetration tester, why would you find this abnormal?
What is odd about this attack? Choose the best answer.
TCP packets transmitted in either direction after the initial three-way handshake will have which of the following bit set?
What type of encryption does WPA2 use?
Yancey is a network security administrator for a large electric company. This company provides power for over 100, 000 people in Las Vegas. Yancey has worked for his company for over 15 years and has become very successful. One day, Yancey comes in to work and finds out that the company will be downsizing and he will be out of a job in two weeks. Yancey is very angry and decides to place logic bombs, viruses, Trojans, and backdoors all over the network to take down the company once he has left. Yancey does not care if his actions land him in jail for 30 or more years, he just wants the company to pay for what they are doing to him. What would Yancey be considered?
Which of the following Trojans would be considered ' Botnet Command Control Center ' ?
What is the command used to create a binary log file using tcpdump?
Fred is the network administrator for his company. Fred is testing an internal switch. From an external IP address, Fred wants to try and trick this switch into thinking it already has established a session with his computer. How can Fred accomplish this?
You have chosen a 22 character word from the dictionary as your password. How long will it take to crack the password by an attacker?
In Trojan terminology, what is a covert channel?
Jess the hacker runs L0phtCrack ' s built-in sniffer utility that grabs SMB password hashes and stores them for offline cracking. Once cracked, these passwords can provide easy access to whatever network resources the user account has access to. But Jess is not picking up hashes from the network. Why?
Harold works for Jacobson Unlimited in the IT department as the security manager. Harold has created a security policy requiring all employees to use complex 14 character passwords. Unfortunately, the members of management do not want to have to use such long complicated passwords so they tell Harold ' s boss this new password policy should not apply to them. To comply with the management ' s wishes, the IT department creates another Windows domain and moves all the management users to that domain. This new domain has a password policy only requiring 8 characters.
Harold is concerned about having to accommodate the managers, but cannot do anything about it. Harold is also concerned about using LanManager security on his network instead of NTLM or NTLMv2, but the many legacy applications on the network prevent using the more secure NTLM and NTLMv2. Harold pulls the SAM files from the DC ' s on the original domain and the new domain using Pwdump6.
Harold uses the password cracking software John the Ripper to crack users ' passwords to make sure they are strong enough. Harold expects that the users ' passwords in the original domain will take much longer to crack than the management ' s passwords in the new domain. After running the software, Harold discovers that the 14 character passwords only took a short time longer to crack than the 8 character passwords.
Why did the 14 character passwords not take much longer to crack than the 8 character passwords?
Which of the following is NOT part of CEH Scanning Methodology?
Take a look at the following attack on a Web Server using obstructed URL:
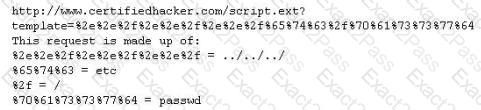
How would you protect from these attacks?
To send a PGP encrypted message, which piece of information from the recipient must the sender have before encrypting the message?
A consultant has been hired by the V.P. of a large financial organization to assess the company ' s security posture. During the security testing, the consultant comes across child pornography on the V.P. ' s computer. What is the consultant ' s obligation to the financial organization?
Frederickson Security Consultants is currently conducting a security audit on the networks of Hawthorn Enterprises, a contractor for the Department of Defense. Since Hawthorn Enterprises conducts business daily with the federal government, they must abide by very stringent security policies. Frederickson is testing all of Hawthorn ' s physical and logical security measures including biometrics, passwords, and permissions. The federal government requires that all users must utilize random, non-dictionary passwords that must take at least 30 days to crack. Frederickson has confirmed that all Hawthorn employees use a random password generator for their network passwords. The Frederickson consultants have saved off numerous SAM files from Hawthorn ' s servers using Pwdump6 and are going to try and crack the network passwords. What method of attack is best suited to crack these passwords in the shortest amount of time?
Bob has a good understanding of cryptography, having worked with it for many years. Cryptography is used to secure data from specific threats, but it does not secure the application from coding errors. It can provide data privacy; integrity and enable strong authentication but it cannot mitigate programming errors. What is a good example of a programming error that Bob can use to explain to the management how encryption will not address all their security concerns?

