Last Update 12 hours ago Total Questions : 191
The Docker Certified Associate (DCA) Exam content is now fully updated, with all current exam questions added 12 hours ago. Deciding to include DCA practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our DCA exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these DCA sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Docker Certified Associate (DCA) Exam practice test comfortably within the allotted time.
You want to provide a configuration file to a container at runtime. Does this set of Kubernetes tools and steps accomplish this?
Solution: Turn the configuration file into a configMap object, use it to populate a volume associated with the pod, and mount that file from the volume to the appropriate container and path.
Are these conditions sufficient for Kubernetes to dynamically provision a persistentVolume, assuming there are no limitations on the amount and type of available external storage?
Solution: A default provisioner is specified, and subsequently a persistentVolumeClaim is created.
The Kubernetes yaml shown below describes a networkPolicy.
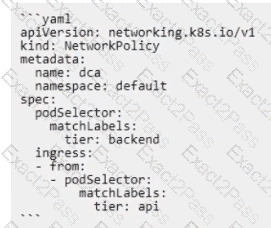
Will the networkPolicy BLOCK this traffic?
Solution: a request issued from a pod bearing the tier: backend label, to a pod bearing the tier: frontend label
Is this a supported user authentication method for Universal Control Plane?
Solution.SAML
Will this configuration achieve fault tolerance for managers in a swarm?
Solution: an odd number of manager nodes, totaling more than two
You want to provide a configuration file to a container at runtime. Does this set of Kubernetes tools and steps accomplish this?
Solution: Mount the configuration file directly into the appropriate pod and container using the .spec.containers.configMounts key.
Will this command list all nodes in a swarm cluster from the command line?
Solution: ' docker swarm nodes '

