Last Update 8 hours ago Total Questions : 81
The Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator content is now fully updated, with all current exam questions added 8 hours ago. Deciding to include NSE7_SSE_AD-25 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our NSE7_SSE_AD-25 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these NSE7_SSE_AD-25 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator practice test comfortably within the allotted time.
Refer to the exhibit.
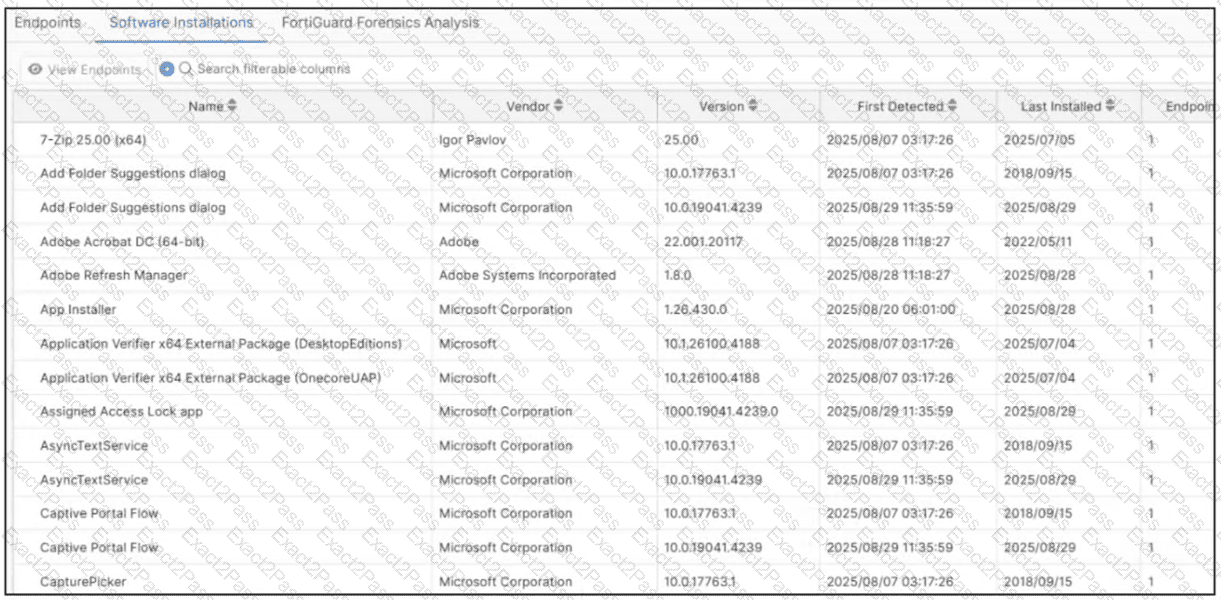
Which type of information or actions are available to a FortiSASE administrator from the following output? (Choose one answer)
Which two statements about FortiSASE Geofencing with regional compliance are true? (Choose two answers)
When you configure FortiSASE Secure Private Access (SPA) with SD-WAN integration, you must establish a routing adjacency between FortiSASE and the FortiGate SD-WAN hub. Which routing protocol must you use?
Refer to the exhibits.
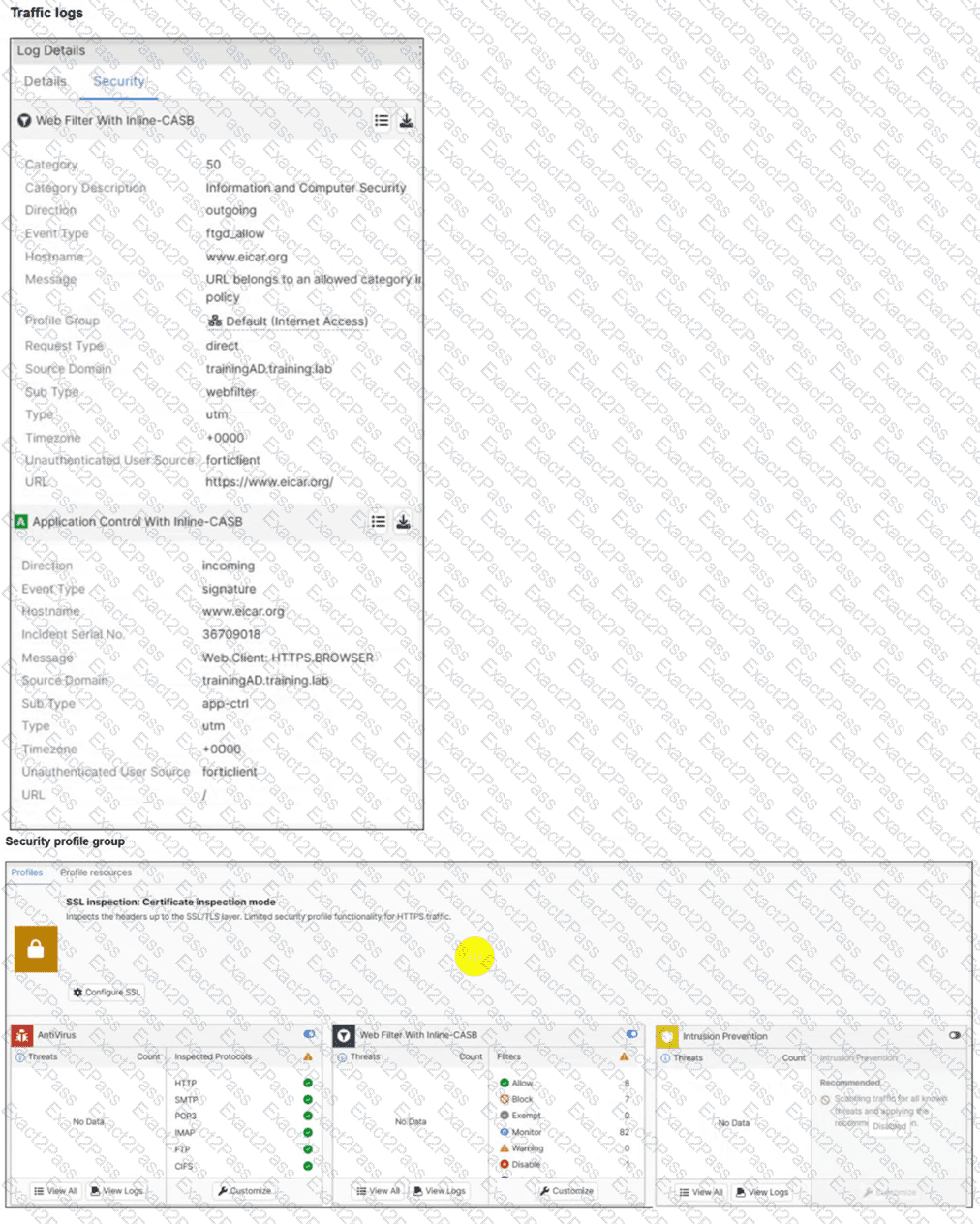
A FortiSASE administrator has configured an antivirus profile in the security profile group and applied it to the internet access policy. Remote users are still able to download the eicar.com-zip file from https://eicar.org.
Which configuration on FortiSASE is allowing users to perform the download? (Choose one answer)
Which authentication method overrides any other previously configured user authentication on FortiSASE?
When viewing the daily summary report generated by FortiSASE. the administrator notices that the report contains very little data. What is a possible explanation for this almost empty report?
What are two benefits of deploying secure private access (SPA) with SD-WAN? (Choose two answers)
How does FortiSASE hide user information when viewing and analyzing logs?
What is the purpose of security posture tagging in ZTNA? (Choose one answer)
What are two advantages of using zero-trust tags? (Choose two.)

