Last Update 4 hours ago Total Questions : 239
The CyberArk Defender - PAM content is now fully updated, with all current exam questions added 4 hours ago. Deciding to include PAM-DEF practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our PAM-DEF exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these PAM-DEF sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CyberArk Defender - PAM practice test comfortably within the allotted time.
During a High Availability node switch you notice an error and the Cluster Vault Manager Utility fails back to the original node.
Which log files should you check to investigate the cause of the issue? (Choose three.)
The password upload utility must run from the CPM server
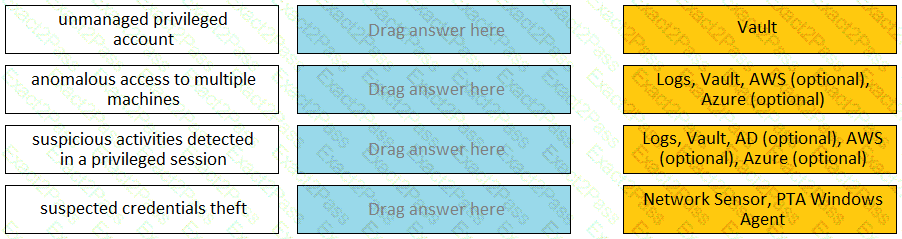
Match each PTA alert category with the PTA sensors that collect the data for it.
In addition to add accounts and update account contents, which additional permission on the safe is required to add a single account?
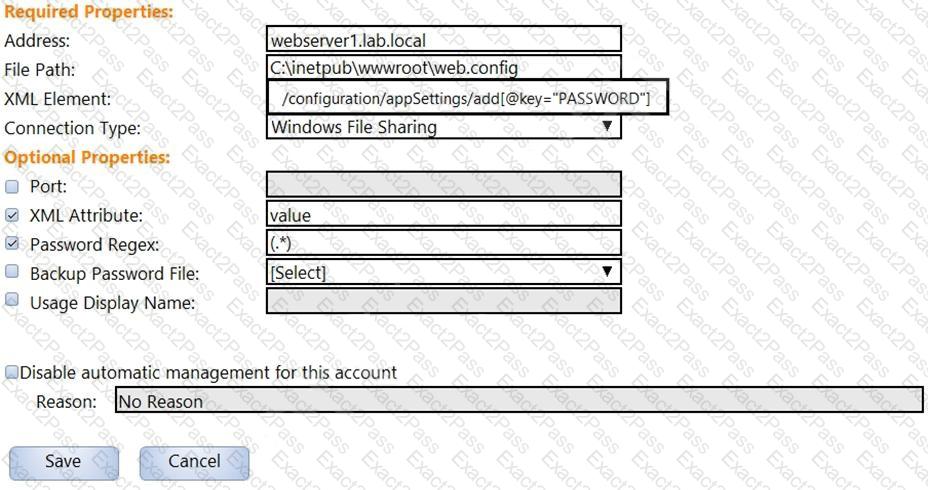
In the screenshot displayed, you just configured the usage in CyberArk and want to update its password.
What is the least intrusive way to accomplish this?
Which parameters can be used to harden the Credential Files (CredFiles) while using CreateCredFile Utility? (Choose three.)
When creating an onboarding rule, it will be executed upon .
A newly created platform allows users to access a Linux endpoint. When users click to connect, nothing happens.
Which piece of the platform is missing?
Where can reconcile and/or logon accounts be linked to an account? (Choose two.)
Which statement about the Master Policy best describes the differences between one-time password and exclusive access functionality?

