Last Update 4 hours ago Total Questions : 239
The CyberArk Defender - PAM content is now fully updated, with all current exam questions added 4 hours ago. Deciding to include PAM-DEF practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our PAM-DEF exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these PAM-DEF sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CyberArk Defender - PAM practice test comfortably within the allotted time.
You have associated a logon account to one your UNIX cool accounts in the vault. When attempting to [b]change [/b] the root account’s password the CPM will…..
Vault admins must manually add the auditors’ group to newly created safes so auditors will have sufficient access to run reports.
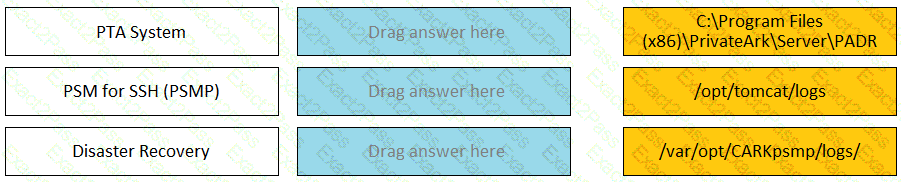
Match each component to its respective Log File location.
Which onboarding method would you use to integrate CyberArk with your accounts provisioning process?
Which CyberArk utility allows you to create lists of Master Policy Settings, owners and safes for output to text files or MSSQL databases?
Assuming a safe has been configured to be accessible during certain hours of the day, a Vault Admin may still access that safe outside of those hours.
An auditor initiates a live monitoring session to PSM server to view an ongoing live session. When the auditor’s machine makes an RDP connection the PSM server, which user will be used?
What is the purpose of the PrivateArk Database service?
Which is the primary purpose of exclusive accounts?
Users can be resulted to using certain CyberArk interfaces (e.g.PVWA or PACLI).

