Last Update 4 hours ago Total Questions : 239
The CyberArk Defender - PAM content is now fully updated, with all current exam questions added 4 hours ago. Deciding to include PAM-DEF practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our PAM-DEF exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these PAM-DEF sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CyberArk Defender - PAM practice test comfortably within the allotted time.
Which of the following Privileged Session Management (PSM) solutions support live monitoring of active sessions?
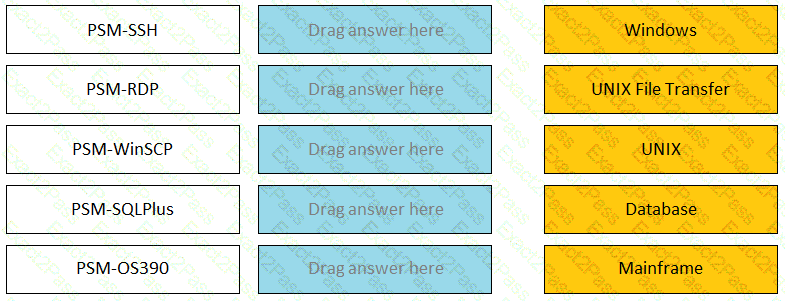
Match the connection component to the corresponding OS/Function.
Ad-Hoc Access (formerly Secure Connect) provides the following features. Choose all that apply.
Which keys are required to be present in order to start the PrivateArk Server service?
Which of the following components can be used to create a tape backup of the Vault?
When should vault keys be rotated?
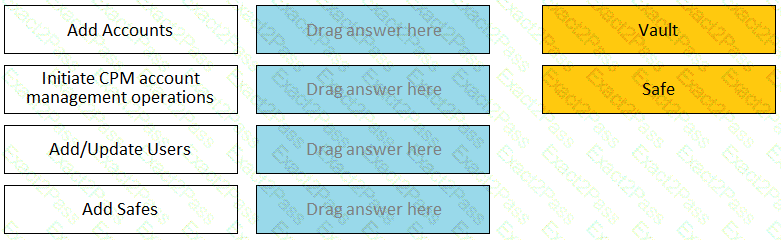
Match each permission to where it can be found.
What is the purpose of a linked account?
Which accounts can be selected for use in the Windows discovery process? (Choose two.)
You have been given the requirement that certain accounts cannot have their passwords updated during business hours.
How can you set up a configuration to meet this requirement?

