Last Update 1 hour ago Total Questions : 227
The Palo Alto Networks Cybersecurity Practitioner (PCCP) content is now fully updated, with all current exam questions added 1 hour ago. Deciding to include Practitioner practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our Practitioner exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these Practitioner sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Palo Alto Networks Cybersecurity Practitioner (PCCP) practice test comfortably within the allotted time.
Which feature is part of an intrusion prevention system (IPS)?
Which type of Software as a Service (SaaS) application provides business benefits, is fast to deploy, requires minimal cost and is infinitely scalable?
Which security function enables a firewall to validate the operating system version of a device before granting it network access?
Which analysis detonates previously unknown submissions in a custom-built, evasion-resistant virtual environment to determine real-world effects and behavior?
Which attacker profile acts independently or as part of an unlawful organization?
What is a dependency for the functionality of signature-based malware detection?
Which service is encompassed by serverless architecture?
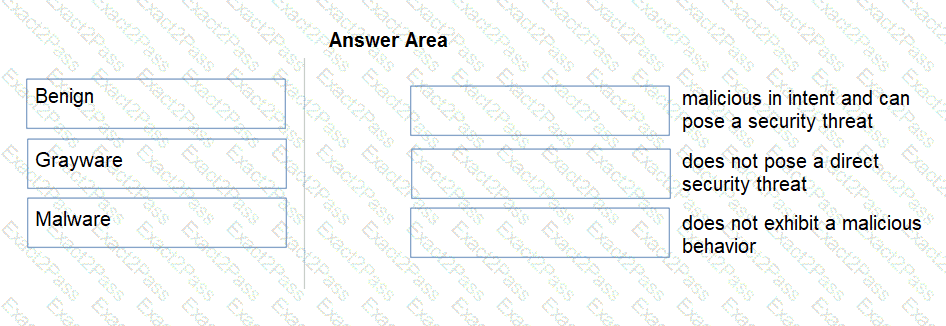
Match the Palo Alto Networks WildFire analysis verdict with its definition.
Which type of LAN technology is being displayed in the diagram?

Under which category does an application that is approved by the IT department, such as Office 365, fall?

