Last Update 9 hours ago Total Questions : 60
The Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity 300-220 CBRTHD content is now fully updated, with all current exam questions added 9 hours ago. Deciding to include 300-220 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 300-220 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 300-220 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity 300-220 CBRTHD practice test comfortably within the allotted time.
Refer to the exhibit.
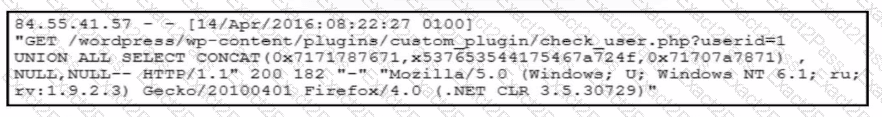
A forensic team must investigate how the company website was defaced. The team isolates the web server, clones the disk, and analyzes the logs. Which technique was used by the attacker initially to access the website?
A SOC team wants to detect lateral movement performed using legitimate administrative tools rather than malware. Which telemetry source provides the MOST reliable visibility for this hunting objective?
During multiple intrusions, analysts observe that attackers consistently perform internal reconnaissance before privilege escalation, avoid noisy exploitation, and limit actions to business hours of the victim’s region. Why is this observation important for attribution?
A SOC team using Cisco security technologies wants to improve its ability to detect threats that bypass traditional security controls by abusing valid user credentials. Which hunting focus MOST effectively addresses this challenge?
After completing several successful hunts using Cisco Secure Network Analytics and Secure Endpoint, the SOC wants to ensure long-term defensive improvement. Which action BEST represents a mature threat hunting outcome?
Refer to the exhibit.
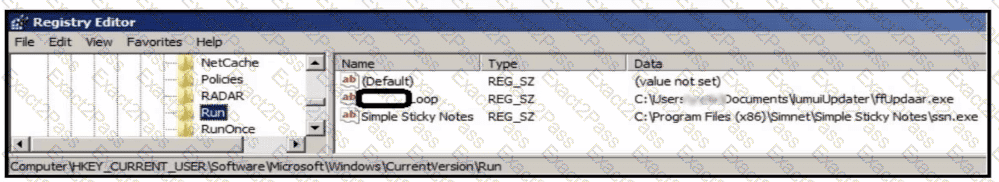
An analyst is evaluating artifacts and logs collected from recent breach. In the logs, ATP established persistency of malware by placing a path to the executable in a specific registry entry. What is the difference between the ATP's approach and using HKEY LOCAL MACHINE\Software\Microsoft\Windows\CurrentVersion\Run instead?
While investigating multiple incidents, analysts notice that attackers consistently use SMB for lateral movement and avoid PowerShell execution. Why is this observation valuable for attribution?
Refer to the exhibit.
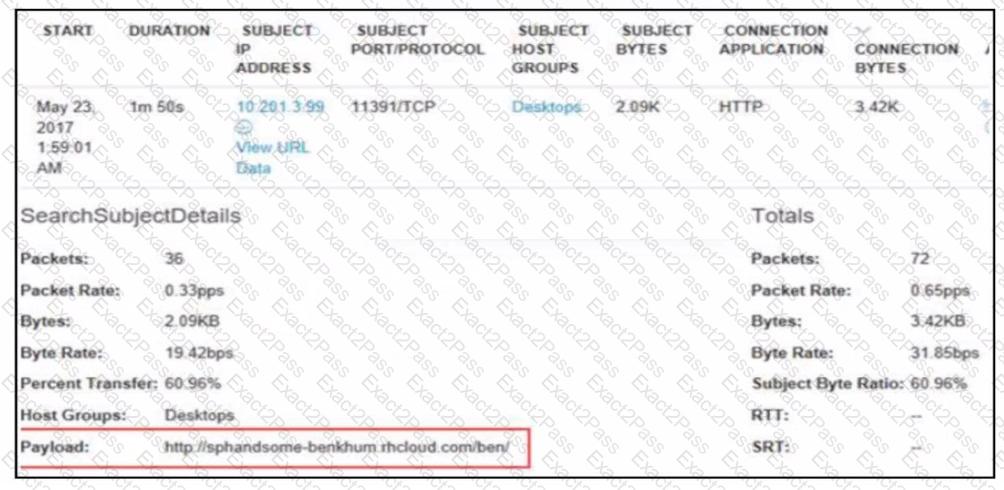
A security analyst receives an alert from Cisco Secure Network Analytics (formerly StealthWatch) with the C2 category. Which information aids the investigation?

