Last Update 17 hours ago Total Questions : 614
The Certified Ethical Hacker Exam content is now fully updated, with all current exam questions added 17 hours ago. Deciding to include 312-50 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 312-50 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 312-50 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Ethical Hacker Exam practice test comfortably within the allotted time.
A large company intends to use Blackberry for corporate mobile phones and a security analyst is assigned to evaluate the possible threats. The analyst will use the Blackjacking attack method to demonstrate how an attacker could circumvent perimeter defenses and gain access to the corporate network. What tool should the analyst use to perform a Blackjacking attack?
Which of the following is an application that requires a host application for replication?
Bluetooth uses which digital modulation technique to exchange information between paired devices?
Which of the following programs is usually targeted at Microsoft Office products?
Which of the following describes the characteristics of a Boot Sector Virus?
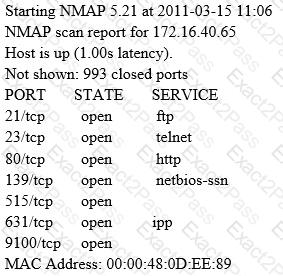
A penetration tester is conducting a port scan on a specific host. The tester found several ports opened that were confusing in concluding the Operating System (OS) version installed. Considering the NMAP result below, which of the following is likely to be installed on the target machine by the OS?
A Security Engineer at a medium-sized accounting firm has been tasked with discovering how much information can be obtained from the firm ' s public facing web servers. The engineer decides to start by using netcat to port 80.
The engineer receives this output:
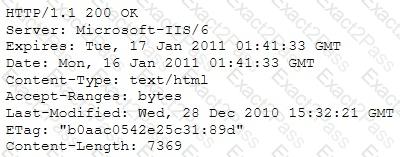
Which of the following is an example of what the engineer performed?
A bank stores and processes sensitive privacy information related to home loans. However, auditing has never been enabled on the system. What is the first step that the bank should take before enabling the audit feature?
Which system consists of a publicly available set of databases that contain domain name registration contact information?
What is one thing a tester can do to ensure that the software is trusted and is not changing or tampering with critical data on the back end of a system it is loaded on?

