Last Update 16 hours ago Total Questions : 139
The Performing CyberOps Using Core Security Technologies (CBRCOR) content is now fully updated, with all current exam questions added 16 hours ago. Deciding to include 350-201 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 350-201 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 350-201 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Performing CyberOps Using Core Security Technologies (CBRCOR) practice test comfortably within the allotted time.
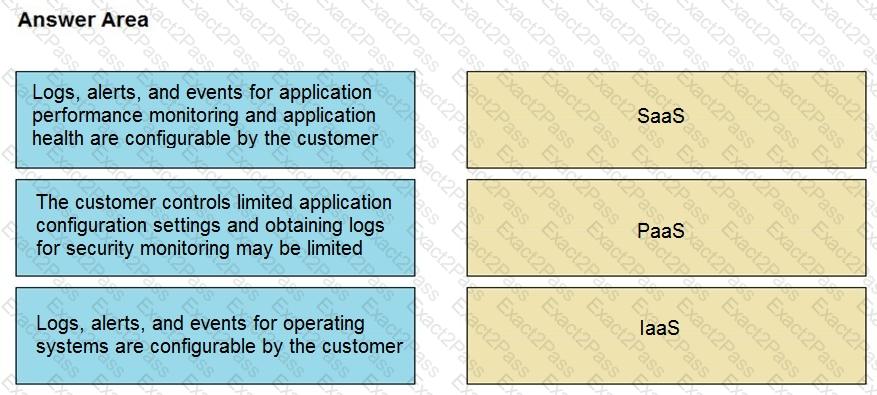
Drag and drop the telemetry-related considerations from the left onto their cloud service models on the right.
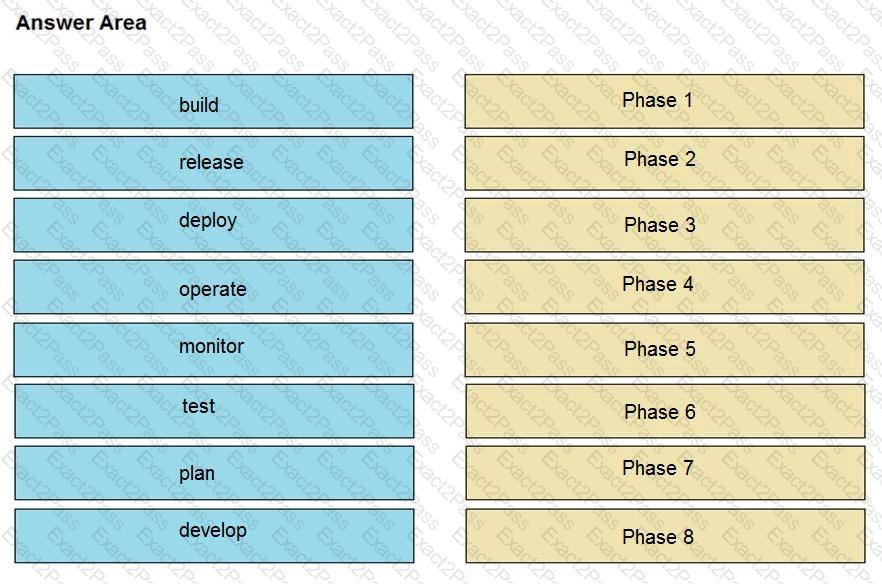
Drag and drop the components from the left onto the phases of the CI/CD pipeline on the right.
A malware outbreak is detected by the SIEM and is confirmed as a true positive. The incident response team follows the playbook to mitigate the threat. What is the first action for the incident response team?
Refer to the exhibit.
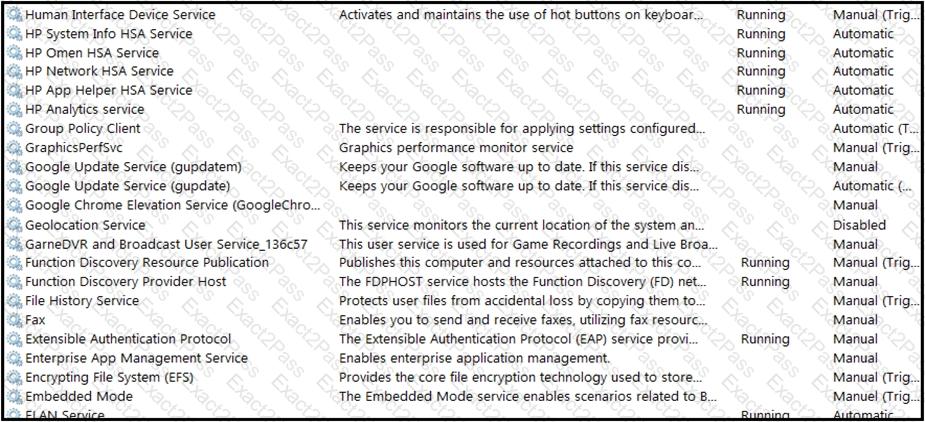
An engineer received multiple reports from employees unable to log into systems with the error: The Group Policy Client service failed to logon – Access is denied. Through further analysis, the engineer discovered several unexpected modifications to system settings. Which type of breach is occurring?
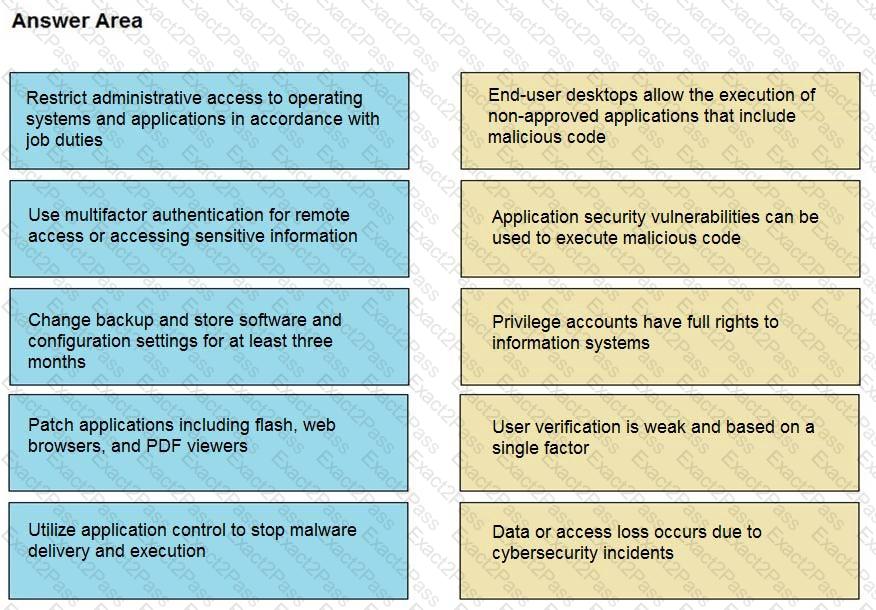
Drag and drop the mitigation steps from the left onto the vulnerabilities they mitigate on the right.
An engineer is developing an application that requires frequent updates to close feedback loops and enable teams to quickly apply patches. The team wants their code updates to get to market as often as possible. Which software development approach should be used to accomplish these goals?
What is a benefit of key risk indicators?
Refer to the exhibit.
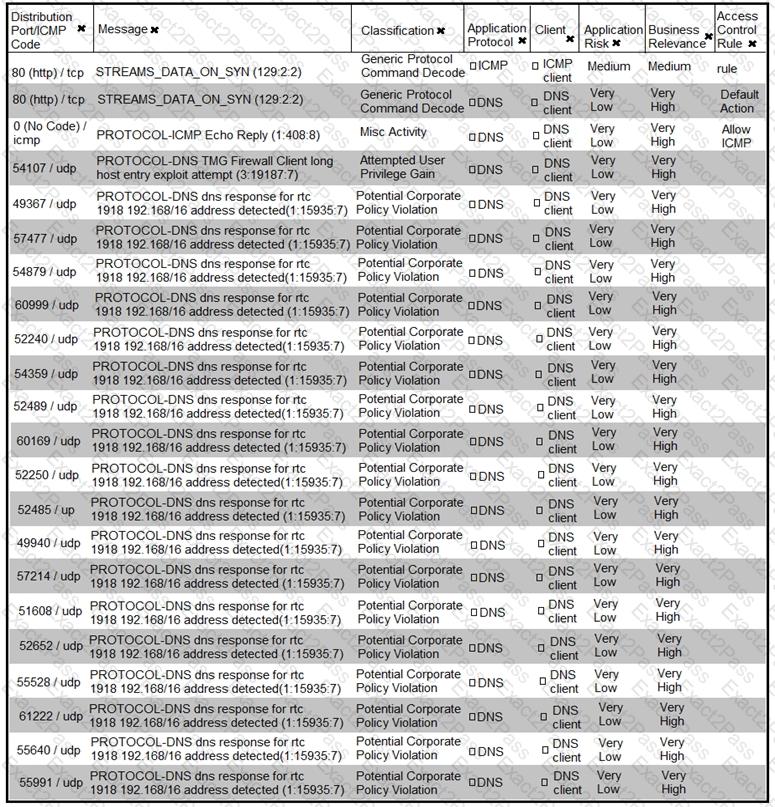
What is the connection status of the ICMP event?
Where do threat intelligence tools search for data to identify potential malicious IP addresses, domain names, and URLs?
Refer to the exhibit.
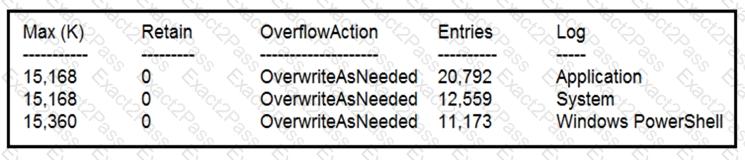
Which command was executed in PowerShell to generate this log?

