Last Update 1 hour ago Total Questions : 434
The Developing Applications using Cisco Core Platforms and APIs (DEVCOR) content is now fully updated, with all current exam questions added 1 hour ago. Deciding to include 350-901 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 350-901 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 350-901 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Developing Applications using Cisco Core Platforms and APIs (DEVCOR) practice test comfortably within the allotted time.
Which transport protocol is used by gNMI?
Which two strategies are used to protect personally identifiable information? (Choose two.)
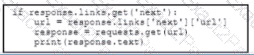
Refer to the exhibit.
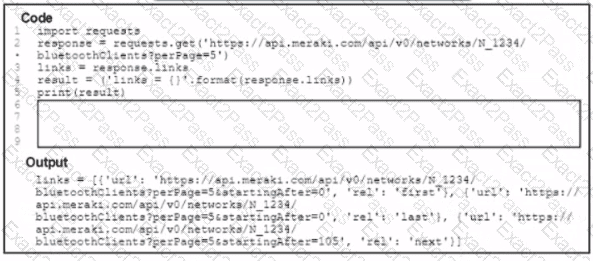
A Python script has these requirements
• Retrieve a list of Bluetooth clients seen by the access pants on a network.
• Print the content of the response
• Retrieve the next page only if it is available in the response headers
What must be added where the code is missing to get the remaining pages by using the next link from the link response header of the last request?
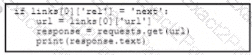
A)
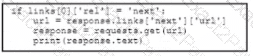
B)
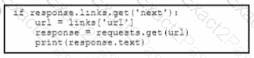
C)
D)
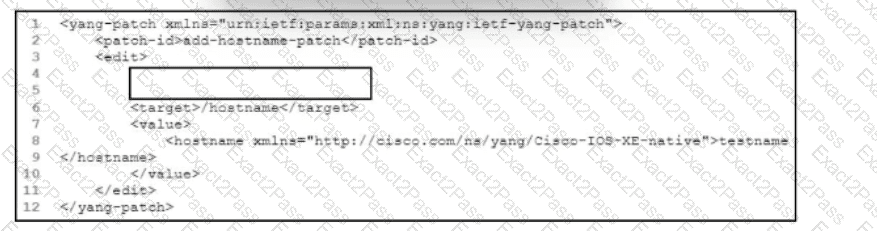
Refer to the exhibit. An engineer must add a new hostname configuration to a Cisco IOS device by using RESTCONF to make a YANG patch request. Which code snippet completes the configuration?
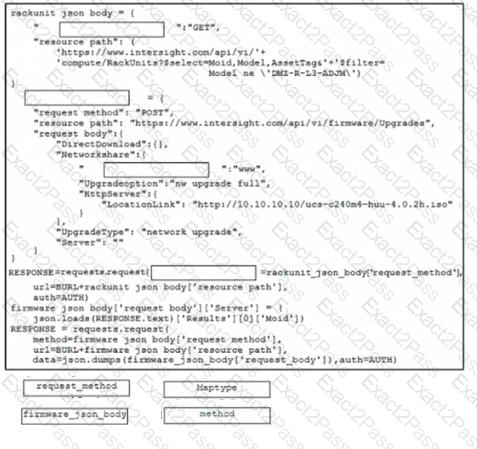
Refer of the exhibit.
Click on the resource labs in the top left corner to view resources to help with this question The script uses the Cisco Intersight REST API Drag and drop the code from the bottom of the code snippet to the blanks in the code to construct a Python script to update the firmware on a specific Cisco interaght managed UCS rack server, DMZ-RL3ADJM.
Refer to the exhibit.

An application ' s REST API GET call is tested to the inventory database. Which missing code must be included to limit
the number of values that are returned from the query to 20?
A developer is working on a bug fix. The existing branch named ‘bugfix05328’ needs to be merged with the current working primary branch named ‘prim404880077’. All changes must be integrated into a single commit instead of preserving them as individual commits. Which git command must be used?
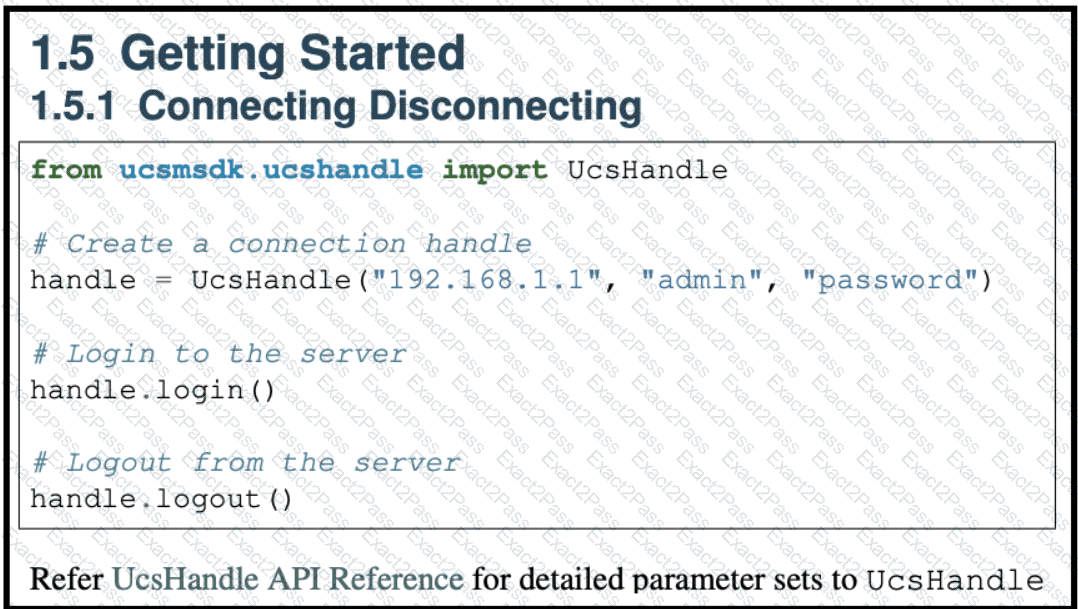
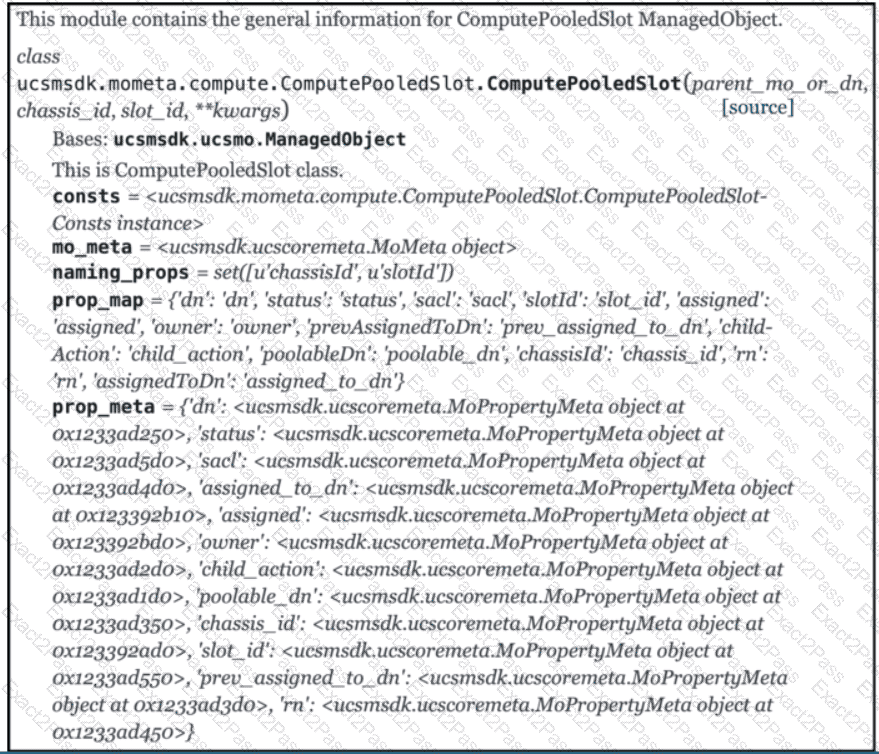
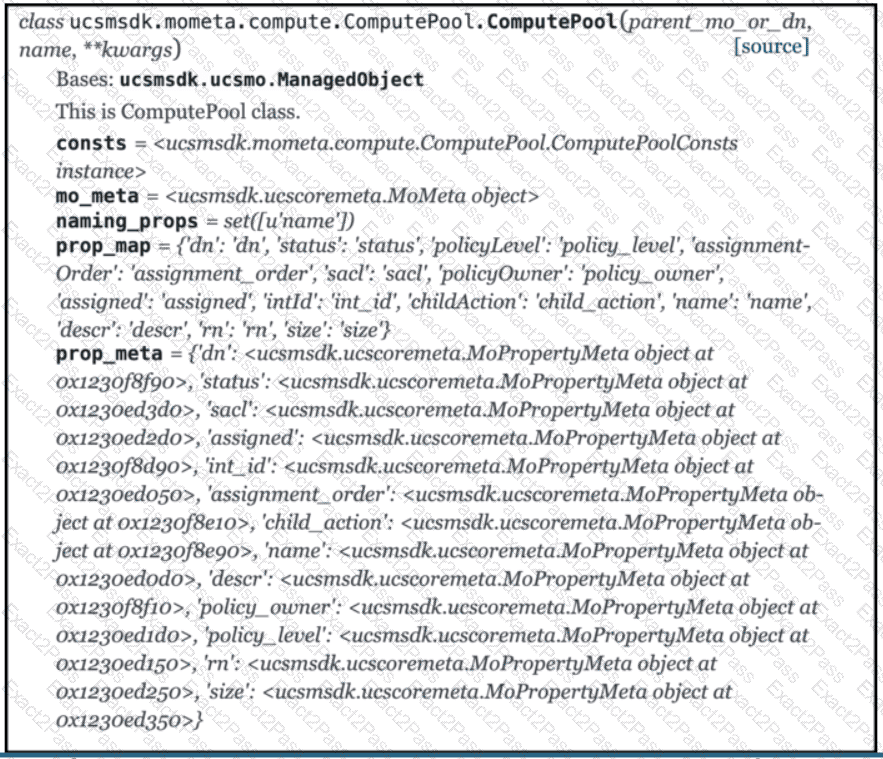
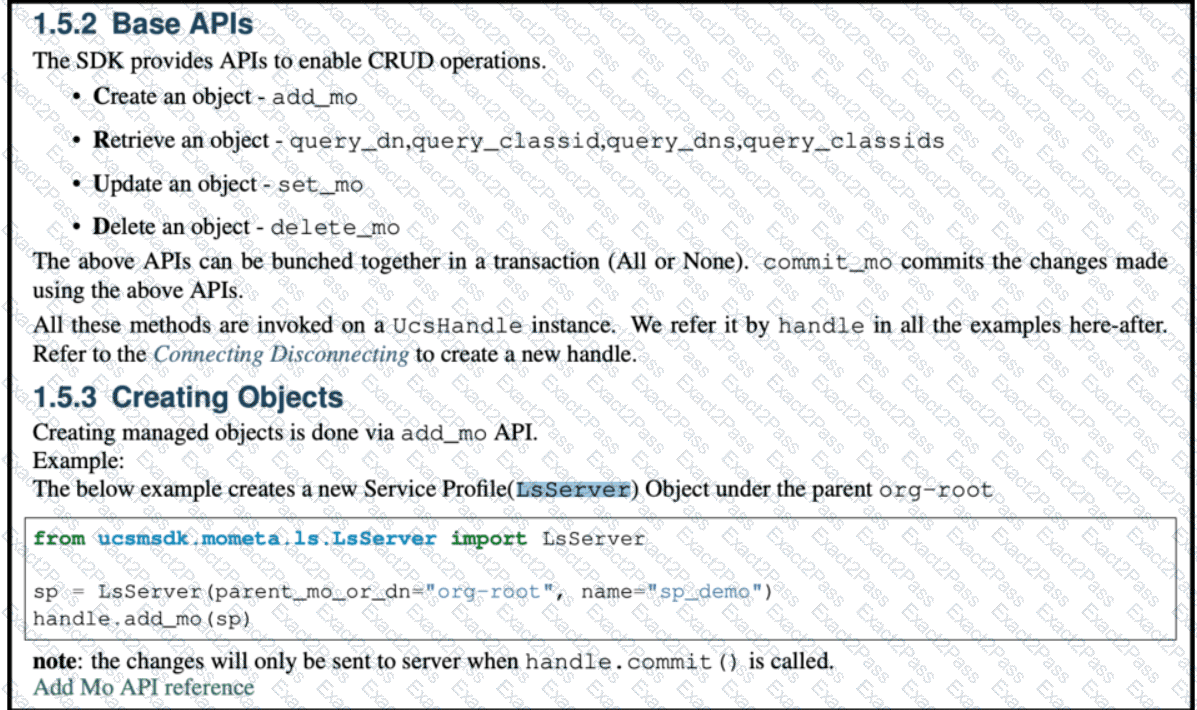
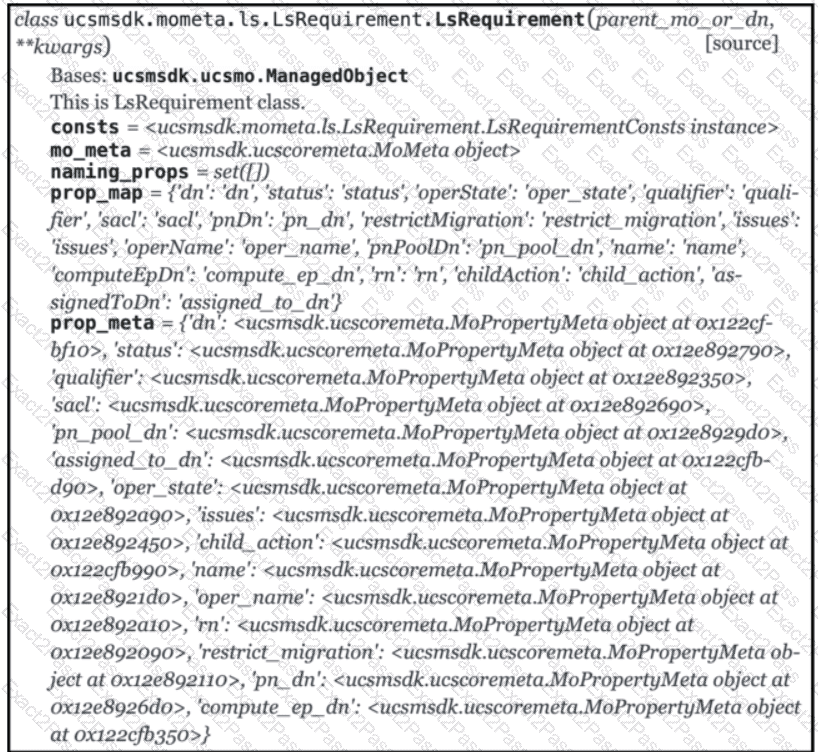
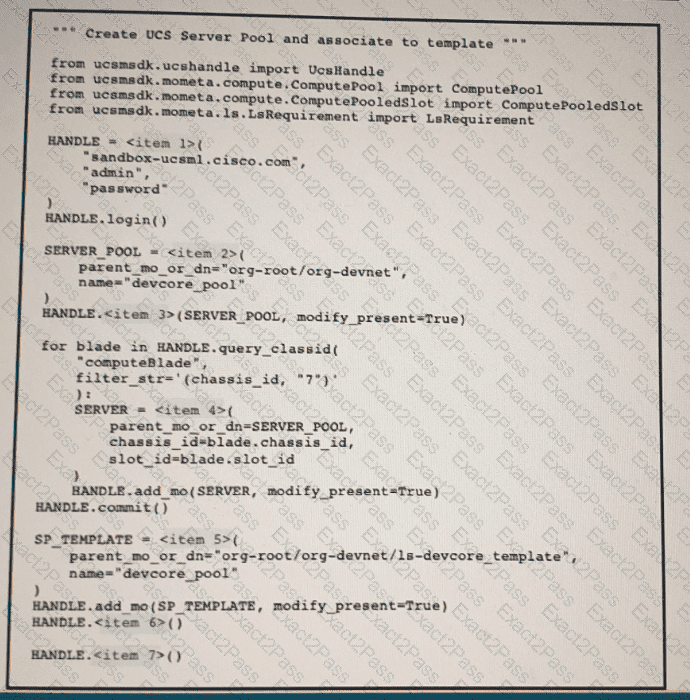
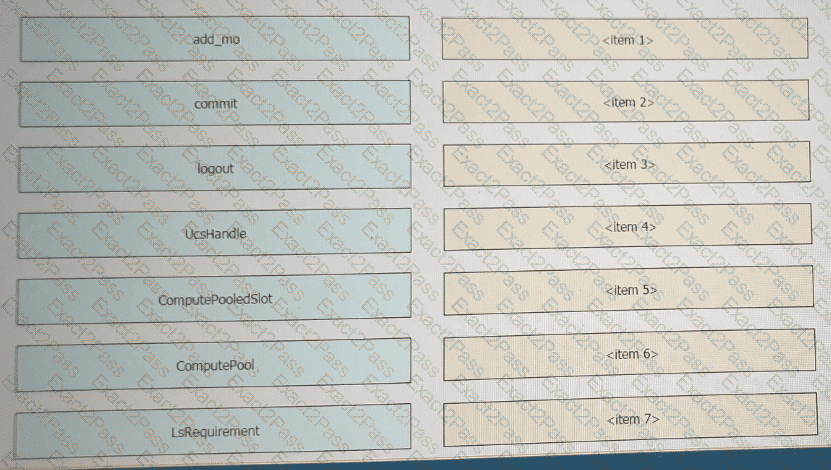
Refer to the exhibit above and click on the resource tabs in the top left corner to view resources to help with this question. Python code using the UCS Python SDK is creating a server pool named “devcore_pool” and populating the pool with all servers from chassis 7 and then the server pool is associated to existing service profile template “devcore_template”. Drag and drop the code snippets from the left onto the item numbers on the right that match the missing sections in the python exhibit.
Refer to the above and click on the resource labs in the top left corner to view resources to help with this question.
Python code using the UCS Python SDK is creating a server pool named " devcore_pool " and populating the pool with all servers from chassis 7, and then the server pool is associated to existing Service Profile template " devcore_template " Drag and drop the code snippets from the left onto the item numbers on the right that match the missing sections in the Python exhibit.
A web application is susceptible to cross-site scripting. Which two methods allow this issue to be mitigated? (Choose two.)
Which two techniques protect against injection attacks? (Choose two.)

