Last Update 15 hours ago Total Questions : 98
The Security, Specialist (JNCIS-SEC) content is now fully updated, with all current exam questions added 15 hours ago. Deciding to include JN0-335 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our JN0-335 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these JN0-335 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Security, Specialist (JNCIS-SEC) practice test comfortably within the allotted time.
How does Juniper ATP Cloud protect a network from zero-day threats?
What are two requirements for enabling AppQoE? (Choose two.)
You want to set up JSA to collect network traffic flows from network devices on your network.
Which two statements are correct when performing this task? (Choose two.)
Which two statements about SRX Series device chassis clusters are correct? (Choose two.)
Which sequence does an SRX Series device use when implementing stateful session security policies using Layer 3 routes?
Which two statements are correct about security policy changes when using the policy rematch feature? (Choose two.)
You are asked to reduce the load that the JIMS server places on your Which action should you take in this situation?
Which two statements are correct about a policy scheduler? (Choose two.)
Exhibit
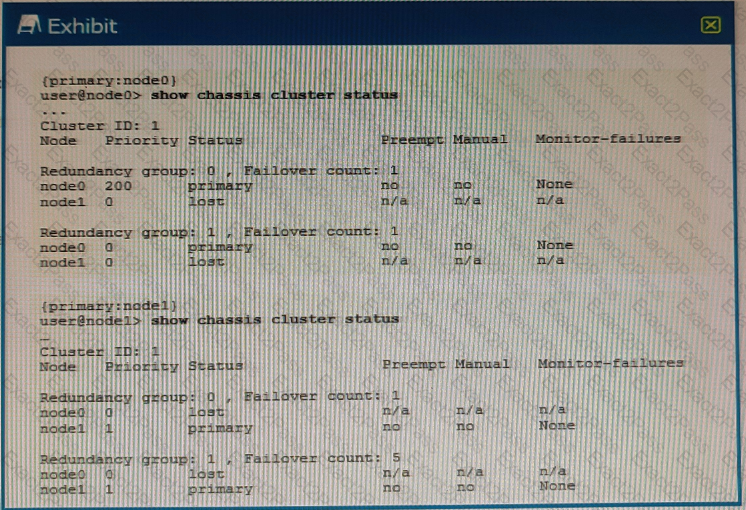
Referring to the exhibit, what do you determine about the status of the cluster.
When a security policy is modified, which statement is correct about the default behavior for active sessions allowed by that policy?

