Last Update 15 hours ago Total Questions : 98
The Security, Specialist (JNCIS-SEC) content is now fully updated, with all current exam questions added 15 hours ago. Deciding to include JN0-335 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our JN0-335 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these JN0-335 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Security, Specialist (JNCIS-SEC) practice test comfortably within the allotted time.
Click the Exhibit button.

You have implemented SSL client protection proxy. Employees are receiving the error shown in the exhibit.
How do you solve this problem?
Your manager asks you to provide firewall and NAT services in a private cloud.
Which two solutions will fulfill the minimum requirements for this deployment? (Choose two.)
Your JIMS server is unable to view event logs.
Which two actions would you take to solve this issue? (Choose two.)
Which two statements are true about Juniper ATP Cloud? (Choose two.)
Which two statements are correct about chassis clustering? (Choose two.)
Exhibit
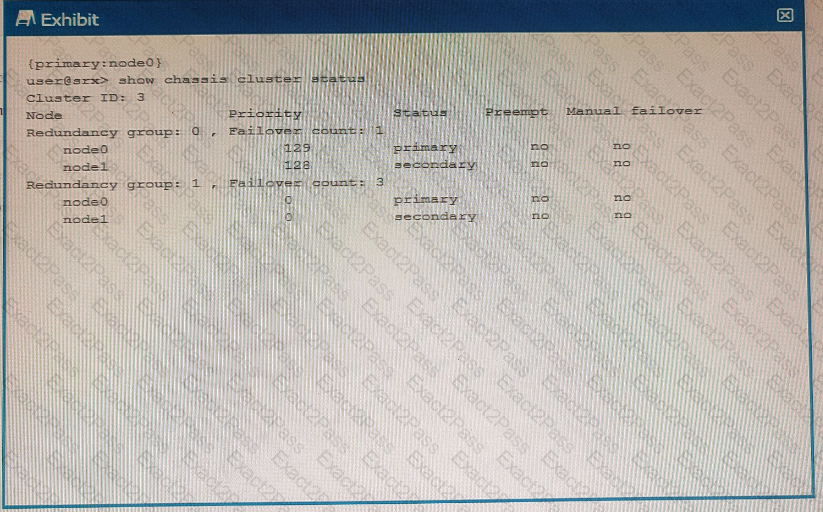
Using the information from the exhibit, which statement is correct?
You are asked to ensure that if the session table on your SRX Series device gets close to exhausting its resources, that you enforce a more aggress.ve age-out of existing flows.
In this scenario, which two statements are correct? (Choose two.)
Which solution enables you to create security policies that include user and group information?
You want to show tabular data for operational mode commands.
In this scenario, which logging parameter will provide this function?

