Last Update 17 hours ago Total Questions : 60
The Palo Alto Networks Network Security Generalist content is now fully updated, with all current exam questions added 17 hours ago. Deciding to include NetSec-Generalist practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our NetSec-Generalist exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these NetSec-Generalist sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Palo Alto Networks Network Security Generalist practice test comfortably within the allotted time.
Which two tools can be used to configure Cloud NGFWs for AWS? (Choose two.)
Which two configurations are required when creating deployment profiles to migrate a perpetual VM-Series firewall to a flexible VM? (Choose two.)
Which action is only taken during slow path in the NGFW policy?
Which action must a firewall administrator take to incorporate custom vulnerability signatures into current Security policies?
What is the main security benefit of adding a CN-Series firewall to an existing VM-Series firewall deployment when the customer is using containers?
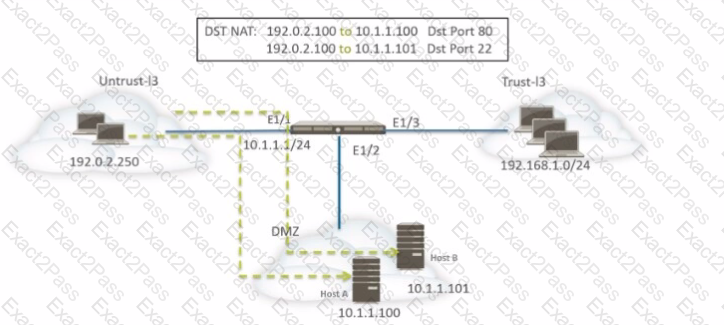
A network administrator is using DNAT to map two servers to one public IP address. Traffic will be directed to a specific server based on the application, where Host A (10.1.1.100) receives HTTP traffic and Host B (10.1.1.101) receives SSH traffic.
Which two sets of Security policy rules will accomplish this configuration? (Choose two.)
Which two components of a Security policy, when configured, allow third-party contractors access to internal applications outside business hours? (Choose two.)
Which firewall attribute can an engineer use to simplify rule creation and automatically adapt to changes in server roles or security posture based on log events?

