Last Update 1 hour ago Total Questions : 434
The Developing Applications using Cisco Core Platforms and APIs (DEVCOR) content is now fully updated, with all current exam questions added 1 hour ago. Deciding to include 350-901 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 350-901 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 350-901 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Developing Applications using Cisco Core Platforms and APIs (DEVCOR) practice test comfortably within the allotted time.
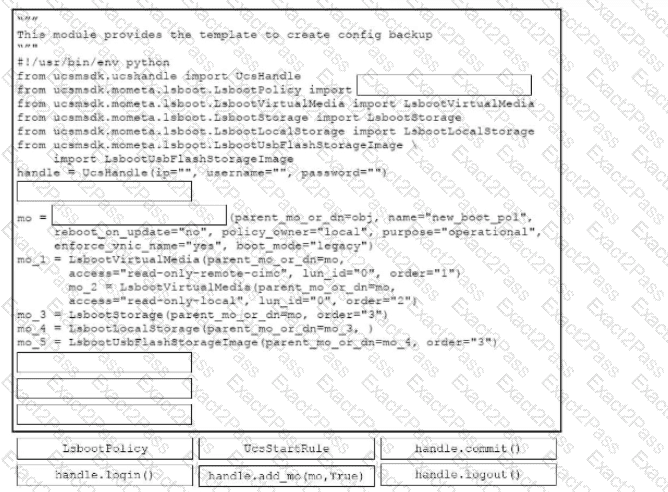
Drag and drop the code snippets from the bottom onto the blanks in the code to create a configuration backup on a Cisco UCS server using the Cisco UCS Python SDK. Some options may be used more than once. Not all options are used.
What is the function of dependency management?
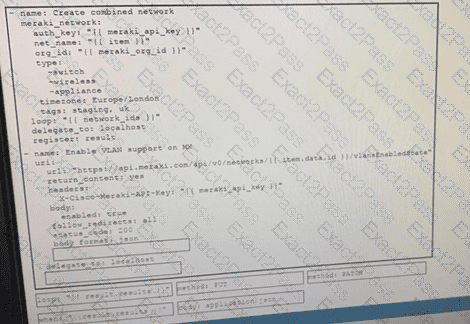
Drag and drop the code from the bottom onto the box where the code is missing on the Ansible task to enable a VLAN on a Meraki MX Device, Not all options are used.
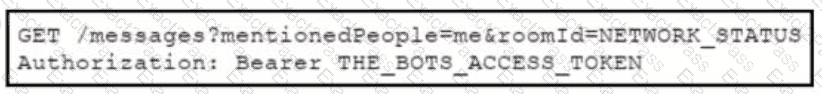
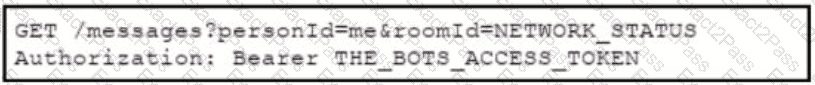
A bot has been created, called " 386231131”, to respond to alarm messages. A developer is now creating a Webhook to allow the bot to respond to messages. Which format allows the Webhook to respond to messages for the bot within Webex Teams?
A)
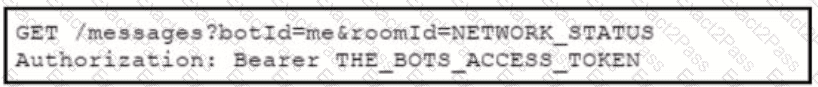
B)

C)
D)
An application has these characteristics
• provide one service or function
• distributed database
• API gateway
• central repository for code
• configuration database
• uses session management
Which two design approaches contribute to the scalability of the application? (Choose two.)
Refer to the exhibit.
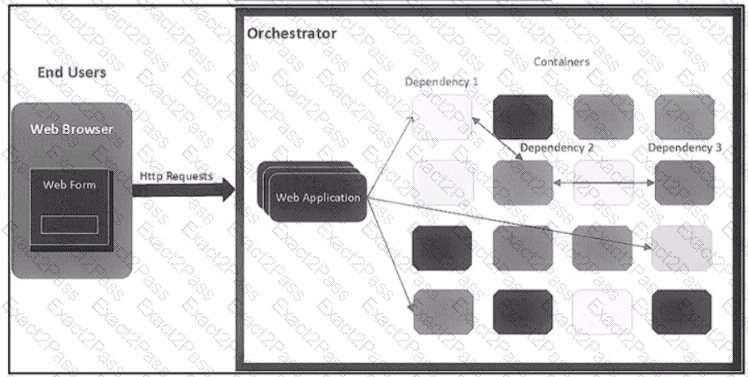
The application follows a containerized microservices architecture that has one container per microservice. The microservices communicate with each other by using REST APIs The double-headed arrows m the diagram display chains of synchronous HTTP calls needed for a single use/request Which action ensures the resilience of the application in the scope of a single user request?
What is a risk to data privacy during the storage and transmission of data?
An application uses OAuth to get access to several API resources on behalf of an end user. What are two valid parameters to send to the authorization server as part of the first step of an authorization code grant flow? (Choose two.)
Refer to the exhibit.
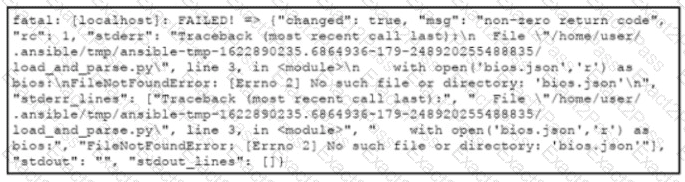
An engineer creates an application that leverages the Ansible framework to provision CPE endpoints that have configuration changes. The application contains an Ansible playbook named provision_cpes.yml that uses the ansible.builtin.script Ansible module to execute these two Python scripts:
• gather and_create.py. which creates a JSON file named bios.json that contains the CPE models and their respective IOS file information
• load and parse.py. which loads the file data and parses it for later consumption
After several successful runs, the application fails. During a review of the Ansible execution logs, the engineer discovers an error output that indicates that one of the stages failed. What is the cause of this issue?
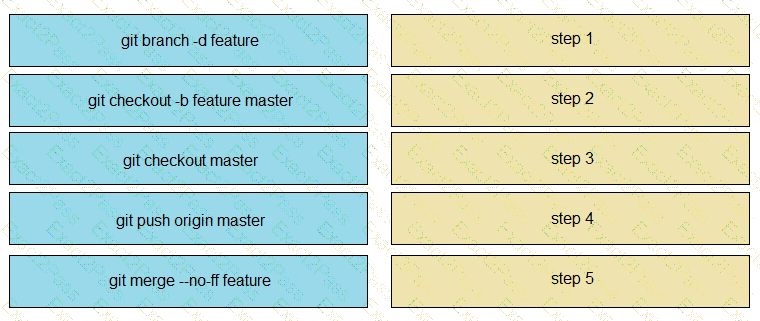
Drag and drop the git commands from the left into the correct order on the right to create a feature branch from the master and then incorporate that feature branch into the master.