Last Update 12 hours ago Total Questions : 115
The Security, Professional (JNCIP-SEC) content is now fully updated, with all current exam questions added 12 hours ago. Deciding to include JN0-637 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our JN0-637 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these JN0-637 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Security, Professional (JNCIP-SEC) practice test comfortably within the allotted time.
You have configured the backup signal route IP for your multinode HA deployment, and the ICL link fails.
Which two statements are correct in this scenario? (Choose two.)
You are asked to see if your persistent NAT binding table is exhausted.
Which show command would you use to accomplish this task?
Which two elements are necessary to configure a rule under an APBR profile? (Choose Two)
Which two statements are correct about automated threat mitigation with Security Director? (Choose two.)
You configured two SRX series devices in an active/passive multimode HA setup.
In this scenario, which statement is correct?
Exhibit:
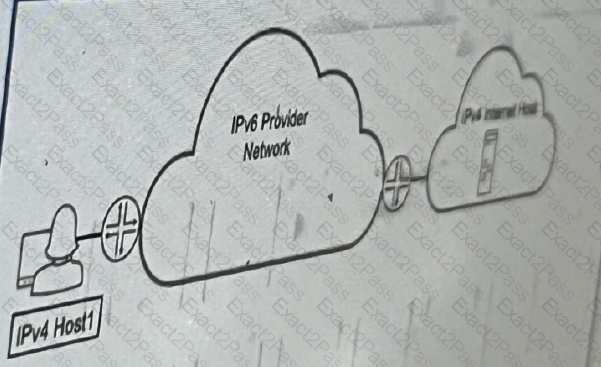
Referring to the exhibit, which technology would you use to provide communication between
IPv4 host1 and ipv4 internal host
Exhibit:
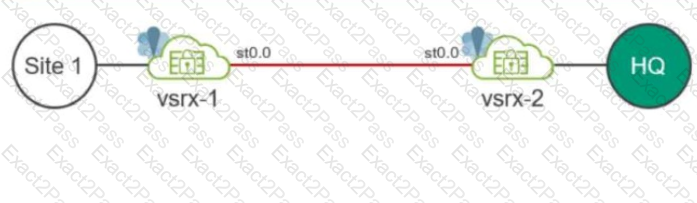
Your company uses SRX Series devices to establish an IPsec VPN that connects Site-1 and the HQ networks. You want VoIP traffic to receive priority over data traffic when it is forwarded across the VPN.
Which three actions should you perform in this scenario? (Choose three.)
What are three configurable monitor components for a service redundancy group? (Choose two)
You are asked to establish a hub-and-spoke IPsec VPN using an SRX Series device as the hub. All of the spoke devices are third-party devices.
Which statement is correct in this scenario?
A customer wants to be able to initiate a return connection to an internal host from a specific
Server.
Which NAT feature would you use in this scenario?

