Last Update 10 hours ago Total Questions : 115
The Security, Professional (JNCIP-SEC) content is now fully updated, with all current exam questions added 10 hours ago. Deciding to include JN0-637 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our JN0-637 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these JN0-637 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Security, Professional (JNCIP-SEC) practice test comfortably within the allotted time.
Referring to the exhibit,
which statement about TLS 1.2 traffic is correct?
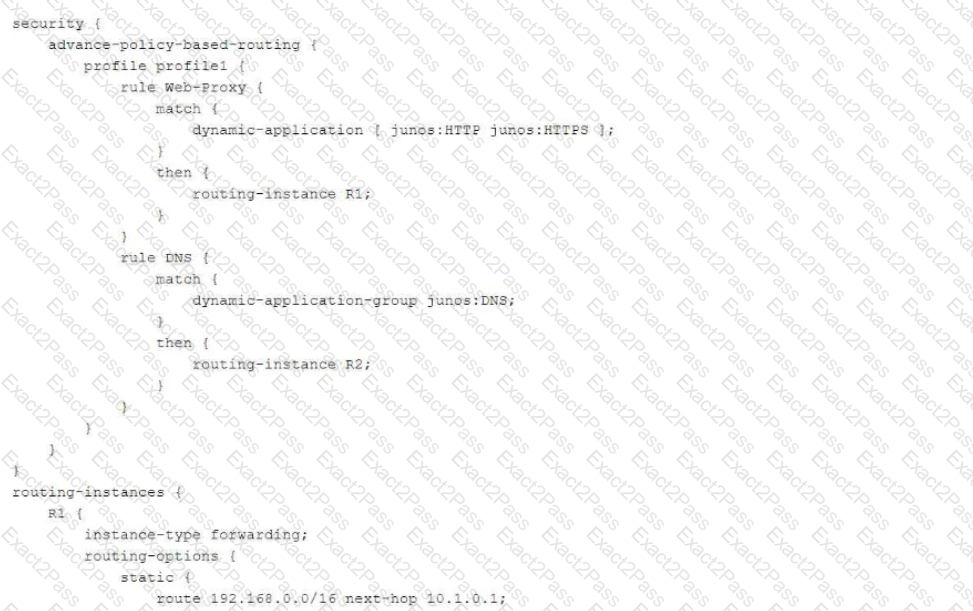
You want to bypass IDP for traffic destined to social media sites using APBR, but it is not working and IDP is dropping the session.
What are two reasons for this problem? (Choose two.)
You are using AutoVPN to deploy a hub-and-spoke VPN to connect your enterprise sites.
In this scenario, which two statements are true? (Choose two.)
Exhibit:
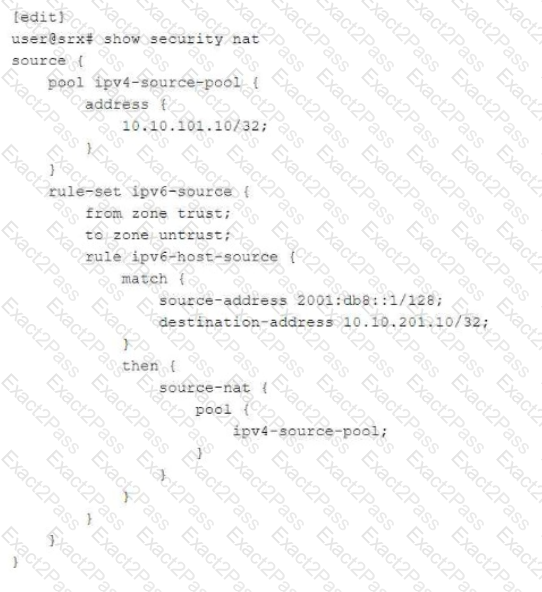
You are configuring NAT64 on your SRX Series device. You have committed the configuration shown in the exhibit. Unfortunately, the communication with the 10.10.201.10 server is not working. You have verified that the interfaces, security zones, and security policies are all correctly configured.
In this scenario, which action will solve this issue?
Referring to the exhibit, you have been assigned the user LogicalSYS1 credentials shown in
the configuration.
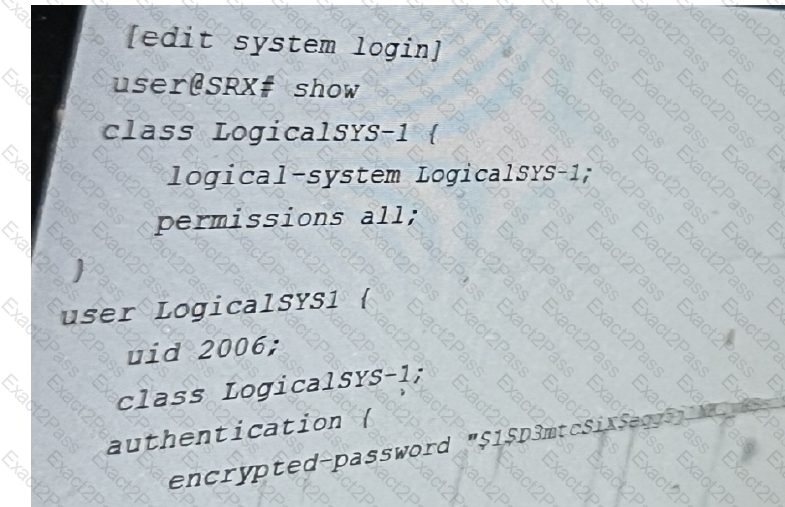
In this scenario, which two statements are correct? (Choose two.)
You need to generate a certificate for a PKI-based site-to-site VPN. The peer is expecting to
user your domain name vpn.juniper.net.
Which two configuration elements are required when you generate your certificate request? (Chose two,)
You want to test how the device handles a theoretical session without generating traffic on the Junos security device.
Which command is used in this scenario?

