Last Update 3 hours ago Total Questions : 131
The Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR) content is now fully updated, with all current exam questions added 3 hours ago. Deciding to include 300-215 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 300-215 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 300-215 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR) practice test comfortably within the allotted time.
During a routine inspection of system logs, a security analyst notices an entry where Microsoft Word initiated a PowerShell command with encoded arguments. Given that the user ' s role does not involve scripting or advanced document processing, which action should the analyst take to analyze this output for potential indicators of compromise?
Refer to the exhibit.
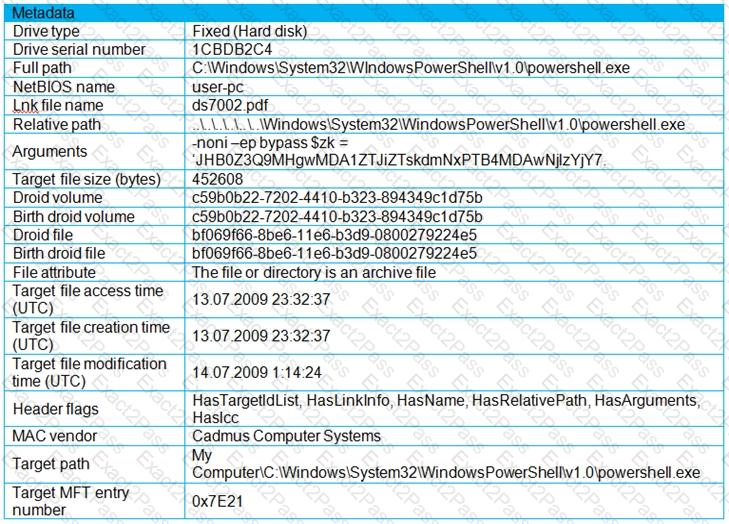
An engineer is analyzing a .LNK (shortcut) file recently received as an email attachment and blocked by email security as suspicious. What is the next step an engineer should take?
Snort detects traffic that is targeting vulnerabilities in files that belong to software in the Microsoft Office suite. On a SIEM tool, the SOC analyst sees an alert from Cisco FMC. Cisco FMC is implemented with Snort IDs. Which alert message is shown?
What can the blue team achieve by using Hex Fiend against a piece of malware?
An organization recovered from a recent ransomware outbreak that resulted in significant business damage. Leadership requested a report that identifies the problems that triggered the incident and the security team’s approach to address these problems to prevent a reoccurrence. Which components of the incident should an engineer analyze first for this report?
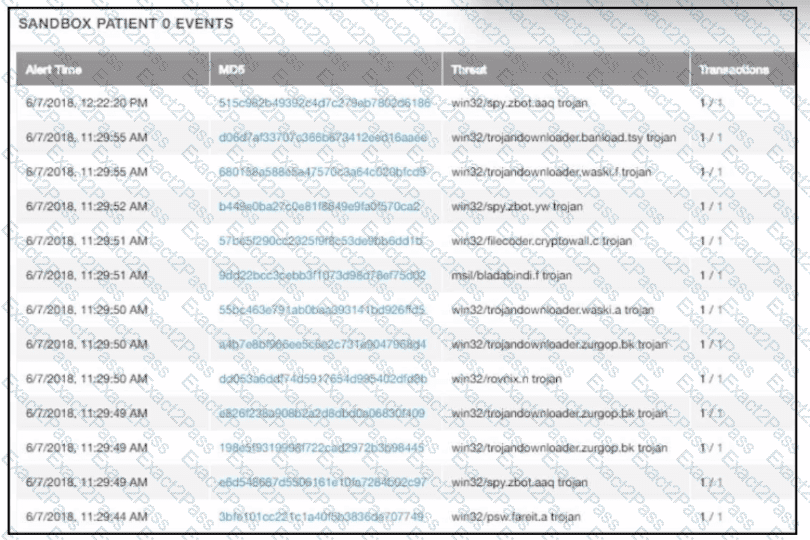
multiple machines behave abnormally. A sandbox analysis reveals malware. What must the administrator determine next?
A security team detected an above-average amount of inbound tcp/135 connection attempts from unidentified senders. The security team is responding based on their incident response playbook. Which two elements are part of the eradication phase for this incident? (Choose two.)
Refer to the exhibit.
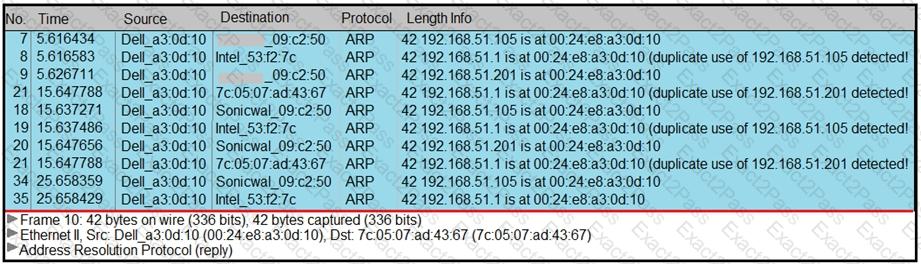
A security analyst notices unusual connections while monitoring traffic. What is the attack vector, and which action should be taken to prevent this type of event?
An engineer must advise on how YARA rules can enhance detection capabilities. What can YARA rules be used to identify?
Refer to the exhibit. 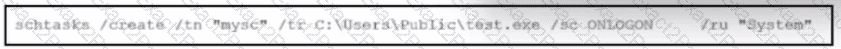
What is occurring?

