We have coached hundreds of principal network architects, infrastructure directors, and senior solutions engineers through this elite expert-tier infrastructure milestone. Let's be completely transparent about this advanced validation process. The candidates who fall short on this intense conceptual evaluation are almost always those who relied on low-tier, unverified test pools—those flat, context-stripped answer repositories floating around public community forums. Those static, superficial memorization shortcuts simply cannot prepare you for the complex business scenario mapping or the high-level design (HLD) trade-offs tested on the real exam. At Ex1eact2Pass, our framework targets the underlying structural logic and technological design lifecycles of the enterprise network framework instead. Our 400-007 CCDE exam prep delivers comprehensive structural and discovery breakdowns for every multi-region plane routing and business alignment query. You will master actual core architectural engineering instead of leaning on short-sighted memorization shortcuts. We map out end-to-end IP traffic patterns, software-defined SD-WAN underlays, cross-border data sovereignty parameters, and complex cloud service placement strategies step by step. Our learning material is built from the ground up by active network expert design authorities who orchestrate global corporate architectures daily. Because of that, we completely avoid mindless, repetitive question lists. Instead, our platform acts as a dynamic workspace that forces you to evaluate infrastructure scaling, regulatory compliance, and protocol dependencies like a principal systems architect. You will learn the exact reason why a specific control plane architecture or security enforcement mechanism succeeds or breaks under heavy corporate business requirements. That is how you build real confidence before logging into the official Pearson VUE and OnVUE testing environment. Our adaptive testing engine develops deep architectural skills that transfer perfectly to live data center deployments, helping you pass on your very first try.
Setting a specific goal for throughput based on per-second data rates between end hosts does not identify the requirements for specific applications When specifying throughput goals for applications, it is important to understand the throughput requirements for each application Which two factors that can constrain application layer throughput? (Choose two.)
The goal for any network designer is to strive to build a resilient network that adapts to changing conditions rapidly with minimal impact on the services running over the network A resilient network can adapt to failures but which soft failure can be harder to define and detect?
A software-defined network can be defined as a network with an API that allows applications to understand and react to the state of the network in near real time A vendor is building an SDN solution that exposes an API to the RIB and potentially the forwarding engine directly The solution provides off-box processes with the capability to interact with the routing table in the same way as a distributed routing process Which SDN framework model does the solution use?
Compared to data plane traffic, control plane traffic is relatively small in volume, but these flows are critical to the overall functioning of the network infrastructure and to voice and video endpoint well. When designing a QoS policy for a network, which two actions for the network control service-class is recommended? (Choose two)
Which hybrid cloud environment enables businesses to more readily stage data-intensive and time-sensitive tasks closer to the source, which reduces latency, eases networking requirements, and improves data protection?
Refer to the exhibit Which impact of using three or more ABRs between the backbone area and area 1 is true?
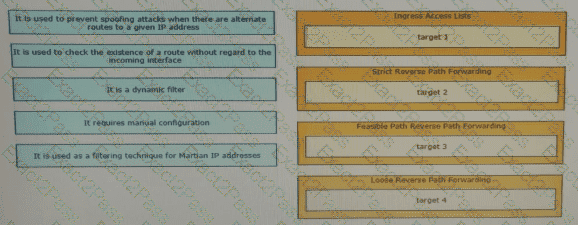
Drag and drop the design characteristics from the left onto the correct network filter techniques on the right. Not all options are used.
The PaaS model provides customers with a virtualized application development platform without the need for them to furnish hardware or system administration using in-house resources All necessary infrastructure components and application development services are provided and managed by the cloud service provider. Which limitation should be considered when selecting PaaS model?
A bank has two data centers (Primary and DR), and compliance policies mandate that services or servers can be moved seamlessly between the two data centers. Additionally, the technology cannot be locked to a specific vendor and must offer good scalability with broad support of layer 2 protocols. Which protocol meets these requirements?
An architect receives a business requirement from a CTO that states the RTO and RPO for a new system should be as close as possible to zero. Which replication method and data center technology should be used?

