Last Update 16 hours ago Total Questions : 344
The CompTIA SecurityX Certification Exam content is now fully updated, with all current exam questions added 16 hours ago. Deciding to include CAS-005 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CAS-005 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CAS-005 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CompTIA SecurityX Certification Exam practice test comfortably within the allotted time.
During a periodic internal audit, a company identifies a few new, critical security controls that are missing. The company has a mature risk management program in place, and the following requirements must be met:
The stakeholders should be able to see all the risks.
The risks need to have someone accountable for them.
Which of the following actions should the GRC analyst take next?
During a security assessment using an EDR solution, a security engineer generates the following report about the assets in the system:
Initial report:
Device | Type | EDR status | Infection Status
LN002 | Linux SE | Enabled (unmanaged) | Unknown
OWIN23 | Windows 7 | Enabled | Clean
OWIN29 | Windows 10 | Enabled (bypass) | Clean
MAC005 | Mac OS | Enabled | Clean
After five days:
Device | Type | EDR status | Infection Status
LN002 | Linux SE | Enabled (unmanaged) | Unknown
OWIN23 | Windows 7 | Enabled | Clean
OWIN29 | Windows 10 | Enabled (bypass) | Infected
MAC005 | Mac OS | Disabled | Clean
Which of the following most likely enabled the infection?
During a recent audit, a company ' s systems were assessed- Given the following information:
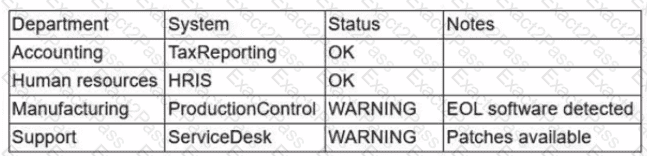
Which of the following is the best way to reduce the attack surface?
After remote desktop capabilities were deployed in the environment, various vulnerabilities were noticed.
• Exfiltration of intellectual property
• Unencrypted files
• Weak user passwords
Which of the following is the best way to mitigate these vulnerabilities? (Select two).
Which of the following best explains the importance of determining organization risk appetite when operating with a constrained budget?
An organization is developing an in-house software platform to support capital planning and reporting functions. In addition to role-based access controls and auditing/logging capabilities, the product manager must include requirements associated with archiving data and immutable backups. Which of the following organizational considerations are most likely associated with this requirement? (Select two)
After a company discovered a zero-day vulnerability in its VPN solution, the company plans to deploy cloud-hosted resources to replace its current on-premises systems. An engineer must find an appropriate solution to facilitate trusted connectivity. Which of the following capabilities is the most relevant?
A security analyst discovered requests associated with IP addresses known for born legitimate 3nd bot-related traffic. Which ofthe following should the analyst use to determine whether the requests are malicious?
Which of the following best describes a common use case for homomorphic encryption?
The material finding from a recent compliance audit indicate a company has an issue with excessive permissions. The findings show that employees changing roles or departments results in privilege creep. Which of the following solutions are the best ways to mitigate this issue? (Select two).
Setting different access controls defined by business area

