Last Update 16 hours ago Total Questions : 344
The CompTIA SecurityX Certification Exam content is now fully updated, with all current exam questions added 16 hours ago. Deciding to include CAS-005 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CAS-005 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CAS-005 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CompTIA SecurityX Certification Exam practice test comfortably within the allotted time.
A security analyst is using data provided from a recent penetration test to calculate CVSS scores to prioritize remediation. Which of the following metric groups would the analyst need to determine to get the overall scores? (Select three).
A company receives reports about misconfigurations and vulnerabilities in a third-party hardware device that is part of its released products. Which of the following solutions is the best way for the company to identify possible issues at an earlier stage?
A company reduced its staff 60 days ago, and applications are now starting to fail. The security analyst is investigating to determine if there is malicious intent for the application failures. The security analyst reviews the following logs:
22:03:50 sshd[21502]: Success login for user01 from 192.168.2.5
22:10:00 sshd[21502]: Failed login for user10 from 192.168.2.5
22:11:40 sshd[21502]: Success login for user07 from 192.168.2.58
22:12:00 sshd[21502]: Failed login for user10 from 192.168.2.5
22:13:00 sshd[21502]: Failed login for user10 from 192.168.2.5
22:13:00 sshd[21502]: Success login for user03 from 192.168.2.27
22:13:00 sshd[21502]: Failed login for user10 from 192.168.2.5
Which of the following is the most likely reason for the application failures?
Which of the following best describes the reason PQC preparation is important?
An organization must provide access to its internal system data. The organization requires that this access complies with the following:
Access must be automated.
Data confidentiality must be preserved.
Access must be authenticated.
Data must be preprocessed before it is retrieved.
Which of the following actions should the organization take to meet these requirements?
Company A and Company D ate merging Company A ' s compliance reports indicate branchprotections are not in place A security analyst needs to ensure that potential threats to the software development life cycle are addressed. Which of the following should me analyst cons < der when completing this basic?
Which of the following AI concerns is most adequately addressed by input sanitation?
A company’s internal network is experiencing a security breach, and the threat actor is still active. Due to business requirements, users in this environment are allowed to utilize multiple machines at the same time. Given the following log snippet:
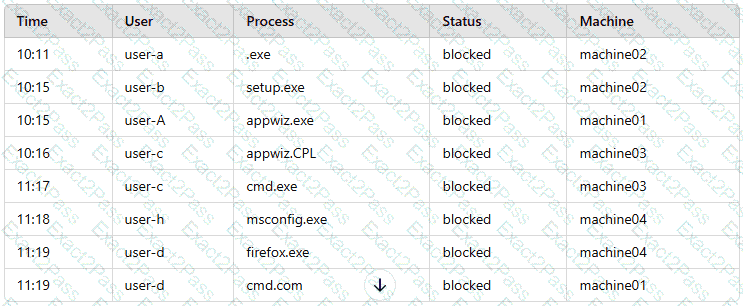
Which of the following accounts should a security analyst disable to best contain the incident without impacting valid users?
A developer receives feedback about code quality and efficiency. The developer needs to identify and resolve the following coding issues before submitting the code changes for peer review:
Indexing beyond arrays
Dereferencing null pointers
Potentially dangerous data type combinations
Unreachable code
Non-portable constructs
Which of the following would be most appropriate for the developer to use in this situation?
A security engineer receives the following findings from a recent security audit:
• Data should be protected based on user permissions and roles.
• User action tracking should be implemented across the network.
• Digital identities should be validated across the data access workflow.
Which of the following is the first action the engineer should take to address the findings?

