Last Update 15 hours ago Total Questions : 344
The CompTIA SecurityX Certification Exam content is now fully updated, with all current exam questions added 15 hours ago. Deciding to include CAS-005 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CAS-005 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CAS-005 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CompTIA SecurityX Certification Exam practice test comfortably within the allotted time.
A company wants to protect against the most common attacks and rapidly integrate with different programming languages. Which of the following technologies is most likely to meet this need?
A security architect for a global organization with a distributed workforce recently received funding lo deploy a CASB solution Which of the following most likely explains the choice to use a proxy-based CASB?
A Chief Information Security Officer (CISO) is concerned that a company ' s current data disposal procedures could result in data remanence. The company uses only SSDs. Which of the following would be the most secure way to dispose of the SSDs given the CISO ' s concern?
A company wants to perform threat modeling on an internally developed, business-critical application. The Chief Information Security Officer (CISO) is most concerned that the application should maintain 99.999% availability and authorized users should only be able to gain access to data they are explicitly authorized to view. Which of the following threat-modeling frameworks directly addresses the CISO ' s concerns about this system?
An organization that performs real-time financial processing is implementing a new backup solution. Given the following business requirements:
The backup solution must reduce the risk of potential backup compromise.
The backup solution must be resilient to a ransomware attack.
The time to restore from backups is less important than backup data integrity.
Multiple copies of production data must be maintained.
Which of the following backup strategies best meets these requirements?
A company is adopting microservice architecture in order to quickly remediate vulnerabilities and deploy to production. All of the microservices run on the same Linux platform. Significant time was spent updating the base OS before deploying code. Which of the following should the company do to make the process efficient?
While reviewing recent modem reports, a security officer discovers that several employees were contacted by the same individual who impersonated a recruiter. Which of the following best describes this type of correlation?
John Doe ' s email account was compromised. The attacker ' s access to John Doe ' s account was removed and MFA was implemented. The attacker convinced Joe Roe in the accounting department to pay a fraudulent invoice through email exchanges. A security analyst is reviewing the headers from the initial email that Joe Roe received:
Received: from 221.15.11.103 (221.15.11.103.mta.com [221.15.11.103])
by with esmtps (TLS 1.2)
Received-SPF: pass
Received: from 18.132.124.10 (18.132.124.10-internal.com [18.132.124.10])
by mx7sgwt-3S (Postfix) with ESMTPS id zRhQ22fmNnQCdys
DKIM-Signature: v=1; c=relaxed/relaxed; d=example.com;
s=default; t=1672873468;
h=To: Message-ID: Date: Content-Type: Subject: From: From: To: Cc: Subject;
To: jroe@example.com
Message-ID: _73/A4-32616-C36L8ZbYC4p
Date: Mon, 07 Apr 2025 +0000
Content-Type: multipart/alternative; boundary=
MIME-Version: 1.0
Reply-To: jdoe@exampl.com
Subject: FW: Invoice
From: jdoe@exampl.com
X-SpamProbability: 0.095349
Which of the following best explains how the attacker was able to get the invoice paid?
After an incident response exercise, a security administrator reviews the following table:
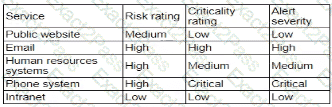
Which of the following should the administrator do to beat support rapid incident response in the future?
An organization is deploying a new data lake that will centralize records from several applications. During the design phase, the security architect identifies the following requirements:
• The sensitivity levels of the data is different.
• The data must be accessed through stateless API calls after authentication.
• Different users will have access to different data sets.
Which of the following should the architect implement to best meet these requirements?

