Last Update 15 hours ago Total Questions : 344
The CompTIA SecurityX Certification Exam content is now fully updated, with all current exam questions added 15 hours ago. Deciding to include CAS-005 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CAS-005 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CAS-005 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CompTIA SecurityX Certification Exam practice test comfortably within the allotted time.
A security engineer reviews an after action report from a previous security breach and notes a long lag time between detection and containment of a compromised account. The engineer suggests using SOAR to address this concern. Which of the following best explains the engineer ' s goal?
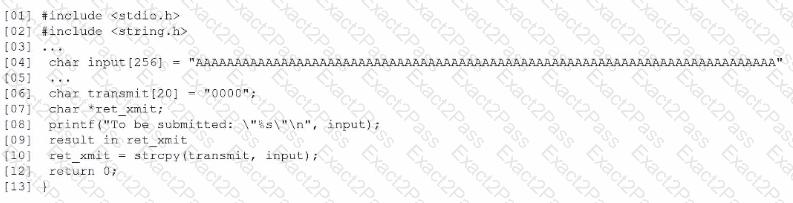
Based on the results of a SAST report on a legacy application, a security engineer is reviewing the following snippet of code flagged as vulnerable:
Which of the following is the vulnerable line of code that must be changed?
A government agency implements a configuration that disables cellular network access on government-issued devices while roaming internationally. The agency issues mobile hot-spots and requires employees to use them for internet access. Which of the following best describes the agency’s rationale?

