Last Update 15 hours ago Total Questions : 344
The CompTIA SecurityX Certification Exam content is now fully updated, with all current exam questions added 15 hours ago. Deciding to include CAS-005 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CAS-005 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CAS-005 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CompTIA SecurityX Certification Exam practice test comfortably within the allotted time.
A compliance officer is reviewing the data sovereignty laws in several countries where the organization has no presence Which of the following is the most likely reason for reviewing these laws?
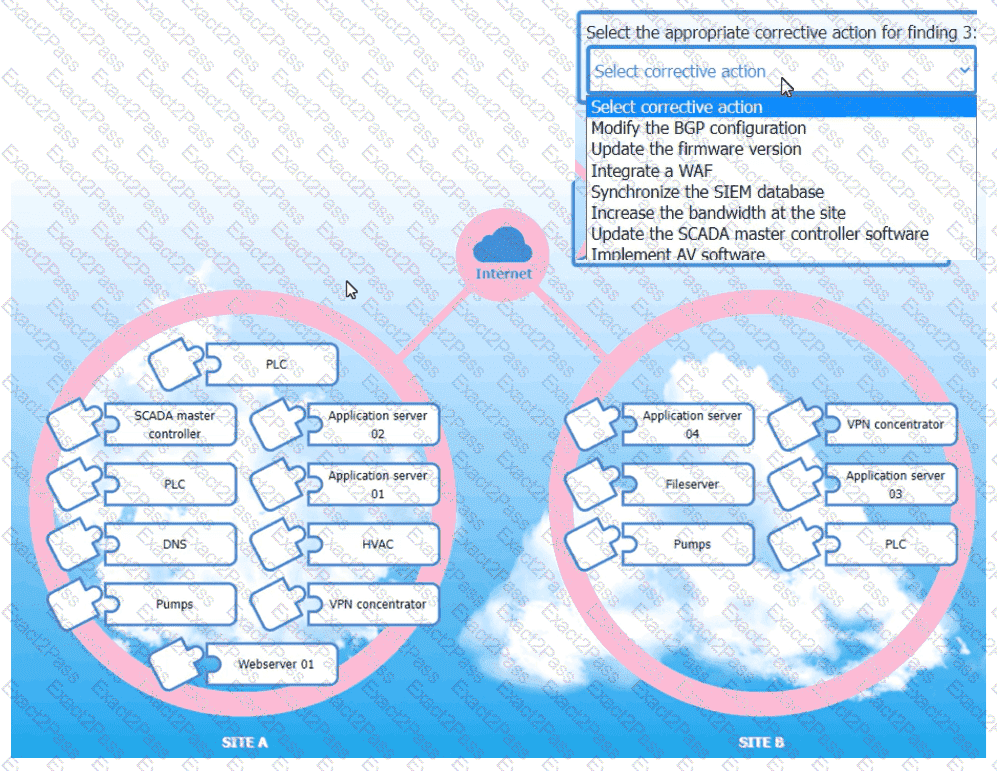
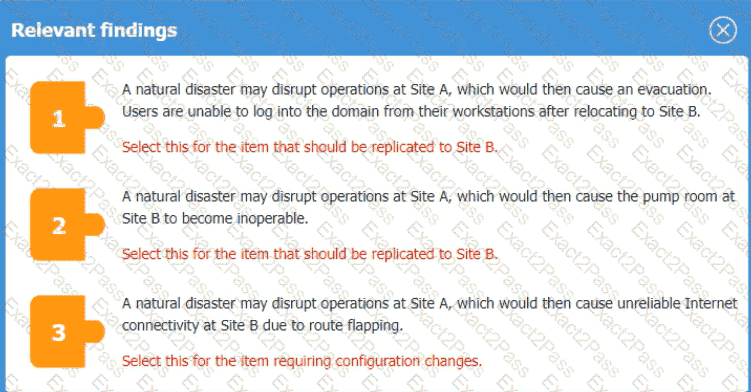
An organization is planning for disaster recovery and continuity ofoperations, and has noted the following relevant findings:
1. A natural disaster may disrupt operations at Site A, which would then cause an evacuation. Users are
unable to log into the domain from-their workstations after relocating to Site B.
2. A natural disaster may disrupt operations at Site A, which would then cause the pump room at Site B
to become inoperable.
3. A natural disaster may disrupt operations at Site A, which would then cause unreliable internet
connectivity at Site B due to route flapping.
INSTRUCTIONS
Match each relevant finding to the affected host by clicking on the host name and selecting the appropriate number.
For findings 1 and 2, select the items that should be replicated to Site B. For finding 3, select the item requiring configuration changes, then select the appropriate corrective action from the drop-down menu.
A security officer received several complaints from usersabout excessive MPA push notifications at night The security team investigates and suspects malicious activities regarding user account authentication Which of the following is the best way for the security officer to restrict MI~A notifications ' '
A security architect must make sure that the least number of services as possible is exposed in order to limit an adversary ' s ability to access the systems. Which of the following should the architect do first?
A penetration tester reviews the following router configuration:
set-system services ssh root login-allow
set-system services web-management https allow
set-system services syslog file interactive
set-system services log mode stream
set-interfaces 0 family inet address 10.12.14.1/8
Which of the following changes is the best way to enhance security?
A SOC analyst must perform threat-modeling activities for a large media organization that has the following characteristics:
The organization maintains operations around the world in support of multiple entertainment networks.
Development activities for the organization ' s web-based platforms occur overseas.
Previous information security failures within the organization have been publicly disclosed.
Which of the following actions is the best for the analyst to consider in the early phases of threat modeling?
A senior security engineer flags the following log file snippet as having likely facilitated an attacker’s lateral movement in a recent breach:
qry_source: 19.27.214.22 TCP/53
qry_dest: 199.105.22.13 TCP/53
qry_type: AXFR
| in comptia.org
------------ directoryserver1 A 10.80.8.10
------------directoryserver2 A 10.80.8.11
------------ directoryserver3 A 10.80.8.12
------------ internal-dns A 10.80.9.1
----------- www-int A 10.80.9.3
------------ fshare A 10.80.9.4
------------ sip A 10.80.9.5
------------ msn-crit-apcs A 10.81.22.33
Which of the following solutions, if implemented, would mitigate the risk of this issue reoccurring?
A security engineer wants to improve the security of an application as part of the development pipeline. The engineer reviews the following component of an internally developed web application that allows employees to manipulate documents from a number of internal servers:
response = requests.get(url)
Users can specify the document to be parsed by passing the document URL to the application as a parameter. Which of the following is the best solution?
A systems administrator is working with clients to verify email-based services are performing properly. The administrator wants to have the email server digitally sign outbound emails using the organization ' s private key. Which of the following should the systems administrator configure?
A systems administrator wants to reduce the number of failed patch deployments in an organization. The administrator discovers that system owners modify systems or applications in an ad hoc manner. Which of the following is the best way to reduce the number of failed patch deployments?

