Last Update 7 hours ago Total Questions : 585
The Certified in Planning and Inventory Management (CPIM 8.0) content is now fully updated, with all current exam questions added 7 hours ago. Deciding to include CPIM-8.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CPIM-8.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CPIM-8.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified in Planning and Inventory Management (CPIM 8.0) practice test comfortably within the allotted time.
An organization recently created a new accounting department, and that department is critical in the event of a disaster for the operations to continue. Which steps should the organization take to create a Business Continuity Plan (BCP)?
Endpoint security needs to be established after an organization procured 1,000 industrial Internet Of Things (IoT) sensors. Which of the following challenges are the security engineers MOST likely to face?
In which of the following circumstances is an organization MOST likely to report the accidental release of personal data to the European Union (EU) General Data Protection Regulation (GDPR) supervisory authority and affected users?
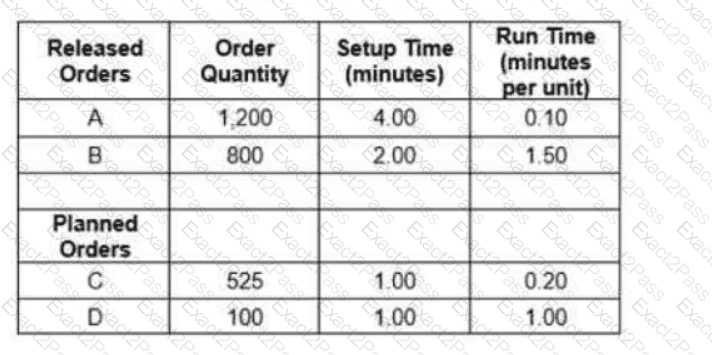
What is the total load requirement for this work center based on the following data?
At which Open Systems Interconnection (OSI) layer does User Datagram Protocol (UDP) function?
Which of the following methods is most often used to manage inventory planning variability across the supply chain?
When considering Defense in Depth (DiD) as part of a network’s architectural design, what is the FIRST layer in a multi-layered defensive strategy?
A Managed Service Provider (MSP) provides hardware and software support for system maintenance and upgrades to a client organization. Who is MOST responsible for auditing security controls related to the hardware and software?
Which of the following is the BEST solution to implement to mitigate the risk of data breach in the event of a lost or stolen mobile device?
Which of the physiological biometric scanning methods is considered the MOST invasive?
Which of the following is the MOST important consideration in a full-scale disaster recovery test?
An organization recently completed an acquisition of another entity and staff members are complaining about the excessive number of credentials they need to remember as each application requires separate logins. This is negatively affecting collaboration efficiency and increasing the risk of human errors. What will the organization consider implementing as part of the solution to improve the situation?
Which of the following is the GREATEST threat for a Border Gateway Protocol (BGP) deployment on the internet?
Improving the performance of a constraint in a job shop environment will:
When assessing a new vendor as a possible business partner, what would BEST demonstrate that the vendor has a proactive approach to data security compliance?

