Last Update 7 hours ago Total Questions : 585
The Certified in Planning and Inventory Management (CPIM 8.0) content is now fully updated, with all current exam questions added 7 hours ago. Deciding to include CPIM-8.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CPIM-8.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CPIM-8.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified in Planning and Inventory Management (CPIM 8.0) practice test comfortably within the allotted time.
An organization has hired a new auditor to review its critical systems infrastructure for vulnerabilities. Which of the following BEST describes the methodology the auditor will use to test whether servers are set up according to the organization ' s documented policies and standards?
Which of the following sampling techniques is BEST suited for comprehensive risk assessments?
Which of the following is a system architecture in a data protection strategy?
Objective security metrics tend to be easier to gather, easier to interpret, and easier to include in reports to management.
What is the BEST objective metric for the effectiveness of a security awareness training?
In which cloud computing model is Identify And Access Management (IAM) the responsibility of a service provider?
A security assessor has been engaged to perform a penetration test on control system components located on a shipping vessel. The individuals on the ship do not have any knowledge of how the component is configured or its internal workings. Which of the following test types does this scenario call for?
A security engineer is responsible for verifying software reliability prior to commercial deployment. Which of the following factor would BEST be verified to ensure that the software stays reliable?
Which of the following strategies is most appropriate for a business unit with a low relative market share in a high-growth market?
An organization has a call center that uses a Voice Over Internet Protocol (VoIP) system. The conversations are sensitive, and the organization is concerned about employees other than the call agents accessing these conversations. What is the MOST effective additional security measure to make?
After a recent threat modeling workshop, the organization has requested that the Chief Information Security Officer (CISO) implement zero trust (ZT) policies. What was the MOST likely threat identified in the workshop?
Which of the following is the BEST way to identify the various types of software installed on an endpoint?
A security team member is assessing an organization’s backup strategy that follows the 3-2-1 rule. How many different types of media should they inspect to validate?
What is the MAIN reason security is considered as part of the system design phase instead of deferring to later phases?
An organization provides customer call center operations for major financial service organizations around the world. As part of a long-term strategy, the organization plans to add healthcare clients to the portfolio. In preparation for contract negotiations with new clients, to which cybersecurity framework(s) should the security team ensure the organization adhere?
Exhibit:
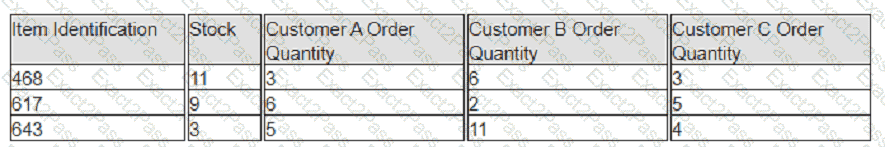
A company has prioritized customers A, B, and C, filling orders in that sequence. What are the impacts to customer service levels for customers B and C?

