Last Update 7 hours ago Total Questions : 585
The Certified in Planning and Inventory Management (CPIM 8.0) content is now fully updated, with all current exam questions added 7 hours ago. Deciding to include CPIM-8.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CPIM-8.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CPIM-8.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified in Planning and Inventory Management (CPIM 8.0) practice test comfortably within the allotted time.
Access Control Lists (ACL), protection bits, and file passwords are typical examples of which of the following access control methods?
Who is responsible for ensuring compliance when an organization uses a cloud provider to host its Virtual Machine (VM) instances?
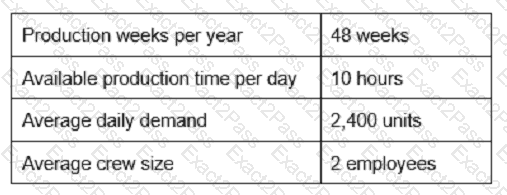
Given the following data, calculate the appropriate takt time:
A firm ' s cash conversion cycle is most likely to improve when the firm:
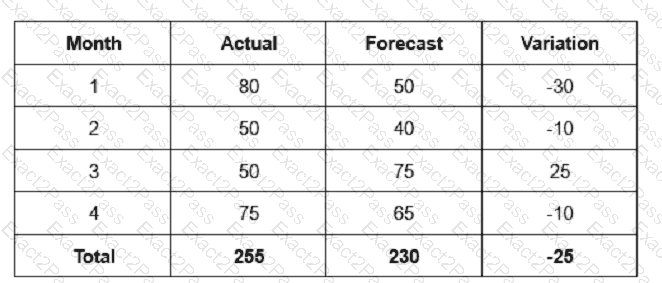
Based on the above table, calculate the mean absolute deviation (MAD).
What document MOST likely states an organization’s values?
Which of the following BEST describes the responsibility of an information System Security Officer?
While conducting penetration testing, one of the testers noticed evidence of additional penetration activities not part of the test. Which of the following is the NEXT course of action for the lead penetration tester?
Which of the following methods places a replenishment order when the quantity on hand falls below a predetermined level?
Which of the following MUST exist for an activity to be considered an audit?
A traffic analysis on an organization ' s network identifies a significant degree of inefficient resource use as a result of broadcast traffic. The organization wants to reduce the scope of the broadcasts without impeding the flow of traffic. Which of the following devices is the BEST choice to implement to achieve this goal?
Which of the following MUST be in place for security to be effective in an organization?
Which of the following systems would be the most cost-efficient for inventory management of a low value item?
Disaster Recovery Plan (DRP) training can be considered complete when the participants
To mitigate risk related to natural disasters, an organization has a separate location with systems and communications in place. Data must be restored on the remote systems before they are ready for use. What type of remote site is this?

