Last Update 7 hours ago Total Questions : 585
The Certified in Planning and Inventory Management (CPIM 8.0) content is now fully updated, with all current exam questions added 7 hours ago. Deciding to include CPIM-8.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CPIM-8.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CPIM-8.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified in Planning and Inventory Management (CPIM 8.0) practice test comfortably within the allotted time.
Moving average forecasting methods are best when demand shows:
A web application is found to have SQL injection (SQLI) vulnerabilities. What is the BEST option to remediate?
Which if the following is the FIRST control step in provisioning user rights and privileges?
An organization wishes to utilize a managed Domain Name System (DNS) provider to reduce the risk of users accessing known malicious sites when web browsing. The organization operates DNS forwarders that forward queries for all external domains to the DNS provider. Which of the following techniques could enable the organization to identify client systems that have attempted to access known malicious domains?
Which of the following techniques would a group use to prioritize problems?
Which of the following is the BEST type of fire extinguisher for a data center environment?
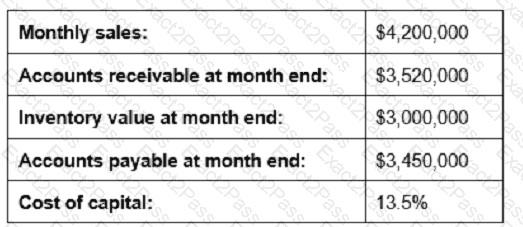
Given the information below, reducing which measure by 10% would contribute most to shortening the cash-to-cash cycle time?
What is the MAIN benefit of network segmentation?
After reviewing the output of a threat modelling workshop, the development manager decides not to implement the application features where issues were identified. What is the BEST description of how the threats from the workshop are being addressed?
In Company XYZ, transaction-costing capability has been Integrated into the shop floor reporting system. A batch of 20 units was started in production. At the fourth operation, 20 units are reported as complete. At the fifth operation, 25 units are reported as complete. When all operations are complete, 20 units are checked into the stockroom. If the error at the fifth operation is undetected, which of the following conditions will be true?
What is a malicious activity that overwhelms a Wireless Access Point (WAP)?
An organization co-locates three divisions and merges them into one network infrastructure. Prior to the merge, the network manager issued devices to employees for remote login. What security concept should be observed to provide security when a device joins the network or when a client makes an Application Programming Interface (API) call?
The Chief Information Security Officer (CISO) defined a requirement to install a network security solution that will have the ability to inspect and block data flowing over network in real time. What network deployment scenario will be MOST suitable?
What is the HIGHEST security concern on trans-border data?
Which of the following is the MAIN element in achieving a successful security strategy?

