Last Update 11 hours ago Total Questions : 356
The Microsoft Identity and Access Administrator content is now fully updated, with all current exam questions added 11 hours ago. Deciding to include SC-300 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our SC-300 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these SC-300 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Microsoft Identity and Access Administrator practice test comfortably within the allotted time.
You need to implement the planned changes for Package1. Which users can create and manage the access review?
You need to locate licenses to the A. Datum users. The solution must need the technical requirements.
Which type of object should you create?
You create a Log Analytics workspace.
You need to implement the technical requirements for auditing.
What should you configure in Azure AD?
You need to meet the planned changes for the User administrator role.
What should you do?
You need to sync the ADatum users. The solution must meet the technical requirements.
What should you do?
Task 10
You need to create a group named Audit. The solution must ensure that the members of Audit can activate the Security Reader role.
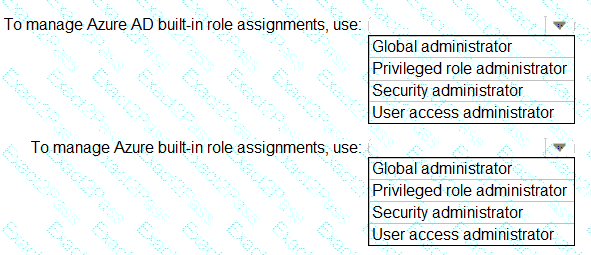
You need to identify which roles to use for managing role assignments. The solution must meet the delegation requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE:Each correct selection is worth one point.