We have coached hundreds of junior systems technicians, desktop support specialists, and aspiring cloud infrastructure engineers through this foundational Cisco milestone. Let's look closely at the modern data center training landscape. The professionals who stumble on this updated v1.1 routing and switching evaluation are almost always those who relied on low-tier test pools—those flat, context-stripped answer repositories floating around public IT forums. Those static, unverified materials simply cannot prepare you for real-world interface configurations or the intricate packet-level troubleshooting tested on the real exam. At Exact2Pass, our approach targets the underlying structural logic, software-defined fabrics, and algorithmic execution patterns of the active Cisco IOS ecosystem instead. Our 200-301 CCNA exam prep delivers comprehensive programmatic breakdowns for every routing table preference and secure wireless access query. You will master actual core switching parameters instead of leaning on short-sighted memorization shortcuts. We map out Rapid PVST+ root bridge elections, VLSM IP allocation boundaries, single-area OSPFv2 neighbor adjacencies, and programmatic API authorization mechanisms step by step. Our learning material is built from the ground up by active network engineering architects who optimize enterprise corporate infrastructure daily. Because of that, we completely avoid mindless, repetitive question-and-answer lists. Instead, our workspace functions as an active training simulation that forces you to evaluate subnet hierarchies, traffic prioritization metrics, and software automation scripts like a seasoned system lead. You will learn the exact reason why a specific VLAN access rule or access control list configuration succeeds or breaks context under production constraints. That is how you build real confidence before logging into the official Pearson VUE and OnVUE testing environment. Our adaptive training software develops genuine technical expertise that transfers perfectly to production engineering sprints, helping you pass on your very first try.
In software-defined architecture, which place handles switching for traffic through a Cisco router?
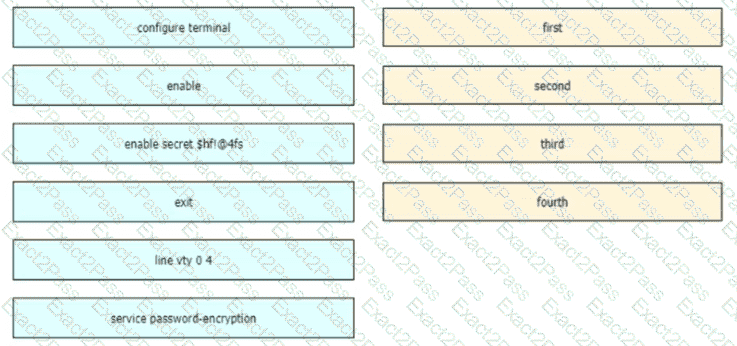
An engineer is configuring an encrypted password for the enable command on a router where the local user database has already been configured Drag and drop the configuration commands from the left into the correct sequence on the right Not all commands are used
How does the dynamically-learned MAC address feature function?
When a site-to-site VPN is configured, which IPsec mode provides encapsulation and encryption of the entire original IP packet?
Refer to the exhibit.
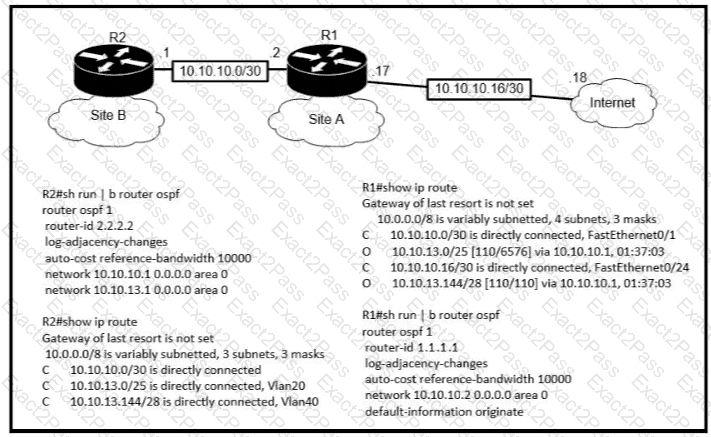
An engineer is bringing up a new circuit to the MPLS provider on the Gi0/1 interface of Router1 The new circuit uses eBGP and teams the route to VLAN25 from the BGP path What s the expected behavior for the traffic flow for route 10.10.13.0/25?
Refer to the exhibit.
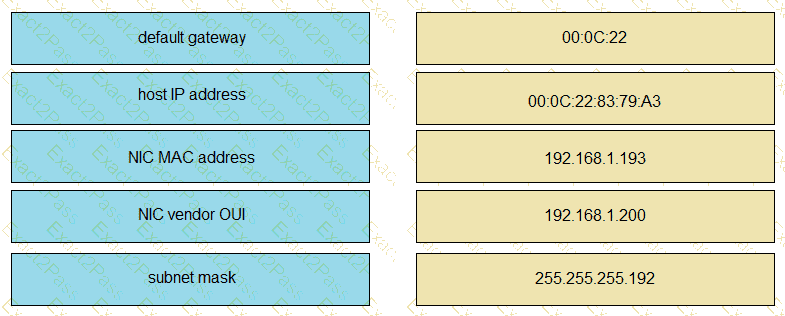
Drag and drop the networking parameters from the left onto the correct values on the right.
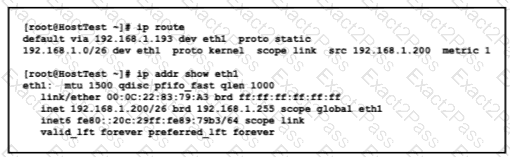
Refer to the exhibit.

An engineer deploys a topology in which R1 obtains its IP configuration from DHCP. If
the switch and DHCP server configurations are complete and correct. Which two sets of commands must be configured on R1 and R2 to complete the task? (Choose two)
Refer to the exhibit.
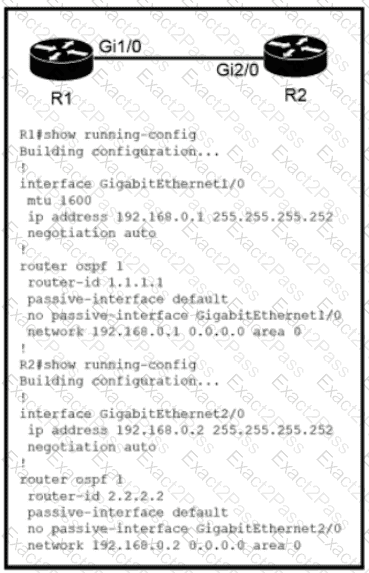
Which configuration issue is preventing the OSPF neighbor relationship from being established between the two routers?
Refer to the exhibit.
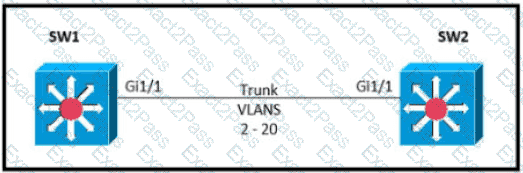
Which command must be executed for Gi1.1 on SW1 to become a trunk port if Gi1/1 on SW2 is configured in desirable or trunk mode?
Drag and drop the DNS lookup components from the left onto the functions on the right.

which IPv6 address block forwards packets to a multicast address rather than a unicast address?
Which unified access point mode continues to serve wireless clients after losing connectivity to the Cisco Wireless LAN Controller?
Refer to the exhibit.
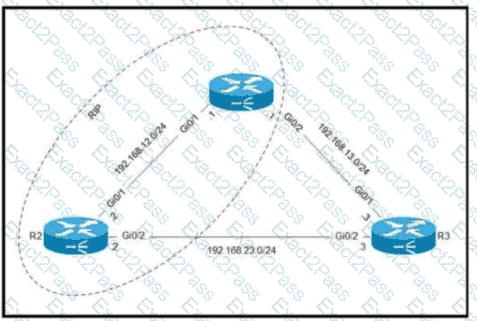
Routers R1 and R2 are configured with RIP as the dynamic routing protocol. A network engineer must configure R1 with a floating static route to serve as a backup route to network 192.168.23.0. Which command must the engineer configure on R1?
When the active router in an HSRP group fails, what router assumes the role and forwards packets?
An engineer requires a scratch interface to actively attempt to establish a trunk link with a neighbor switch. What command must be configured?
How does a Cisco Unified Wireless network respond to Wi-Fi channel overlap?
A corporate office uses four floors in a building
• Floor 1 has 24 users
• Floor 2 has 29 users
• Floor 3 has 28 users
•Floor 4 has 22 users
Which subnet summarizes and gives the most efficient distribution of IP addresses for the router configuration?
What are two similarities between UTP Cat 5e and Cat 6a cabling? (Choose two.)
An engineer must establish a trunk link between two switches. The neighboring switch is set to trunk or desirable mode. What action should be taken?
Which command must be entered when a device is configured as an NTP server?

