Last Update 4 hours ago Total Questions : 476
The Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) content is now fully updated, with all current exam questions added 4 hours ago. Deciding to include 200-201 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 200-201 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 200-201 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) practice test comfortably within the allotted time.
A user received a targeted spear-phishing email and identified it as suspicious before opening the content. To which category of the Cyber Kill Chain model does to this type of event belong?
A malicious file has been identified in a sandbox analysis tool.
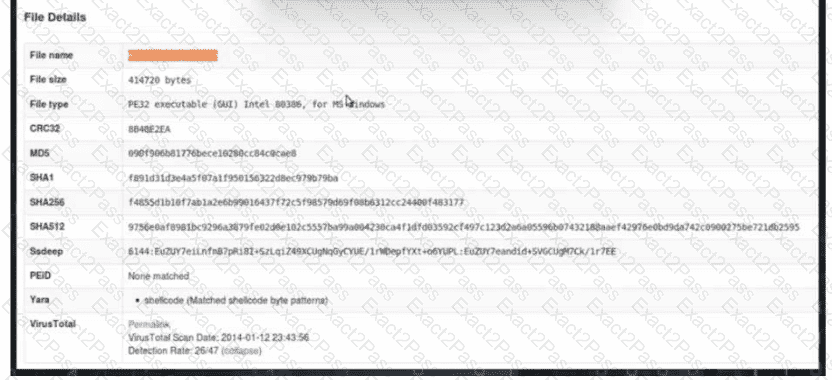
Which piece of information is needed to search for additional downloads of this file by other hosts?
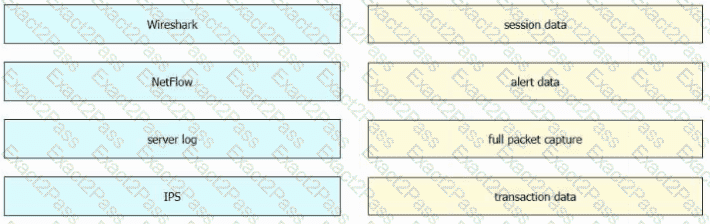
An engineer must gather data for monitoring purposes from different network devices. The engineer needs to collect events from the local network and use that information for packet sniffing. The solution must create an exact copy of traffic and provide full fidelity. Which solution should the engineer use?
Drag and drop the data sources from the left onto the corresponding data types on the right.
A security analyst reviews the firewall and observes the large number of frequent events. The analyst starts the packet capture with the Wireshark and identifies that TCP port reuse was detected incorrectly as a TCP split-handshake attack by the firewall. How must an impact from this event be categorized?
What is the principle of defense-in-depth?
Refer to the exhibit.
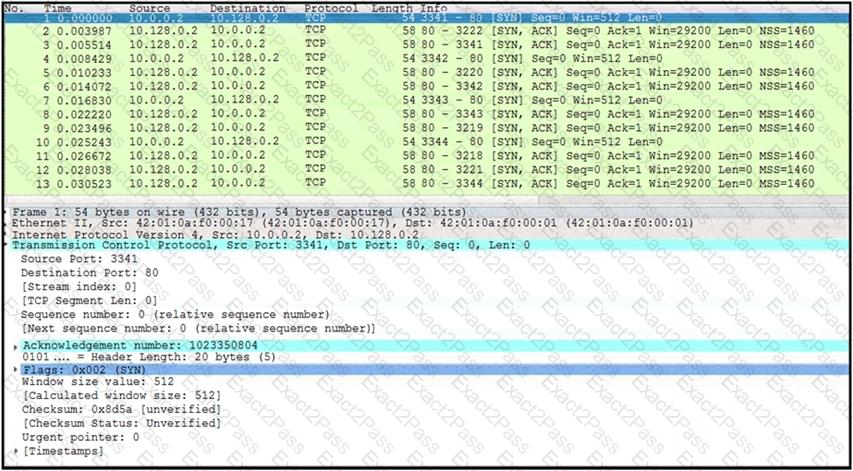
What is occurring in this network traffic?
What is a difference between tampered and untampered disk images?
What is a difference between SI EM and SOAR security systems?
Which two elements are used by the defense-in-depth strategy? (Choose two)

