Last Update 15 hours ago Total Questions : 482
The CompTIA CyberSecurity Analyst CySA+ Certification Exam content is now fully updated, with all current exam questions added 15 hours ago. Deciding to include CS0-003 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CS0-003 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CS0-003 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any CompTIA CyberSecurity Analyst CySA+ Certification Exam practice test comfortably within the allotted time.
A systems administrator notices unfamiliar directory names on a production server. The administrator reviews the directory listings and files, and then concludes the server has been
compromised. Which of the following steps should the administrator take next?
Which of the following most accurately describes the Cyber Kill Chain methodology?
Which of the following is the appropriate phase in the incident response process to perform a vulnerability scan to determine the effectiveness of corrective actions?
Which of following would best mitigate the effects of a new ransomware attack that was not properly stopped by the company antivirus?
Which of the following best describes the reporting metric that should be utilized when measuring the degree to which a system, application, or user base is affected by an uptime availability outage?
A vulnerability scan shows the following issues:
Asset Type
CVSS Score
Exploit Vector
Workstations
6.5
RDP vulnerability
Storage Server
9.0
Unauthorized access due to server application vulnerability
Firewall
8.9
Default password vulnerability
Web Server
10.0
Zero-day vulnerability (vendor working on patch)
Which of the following actions should the security analyst take first?
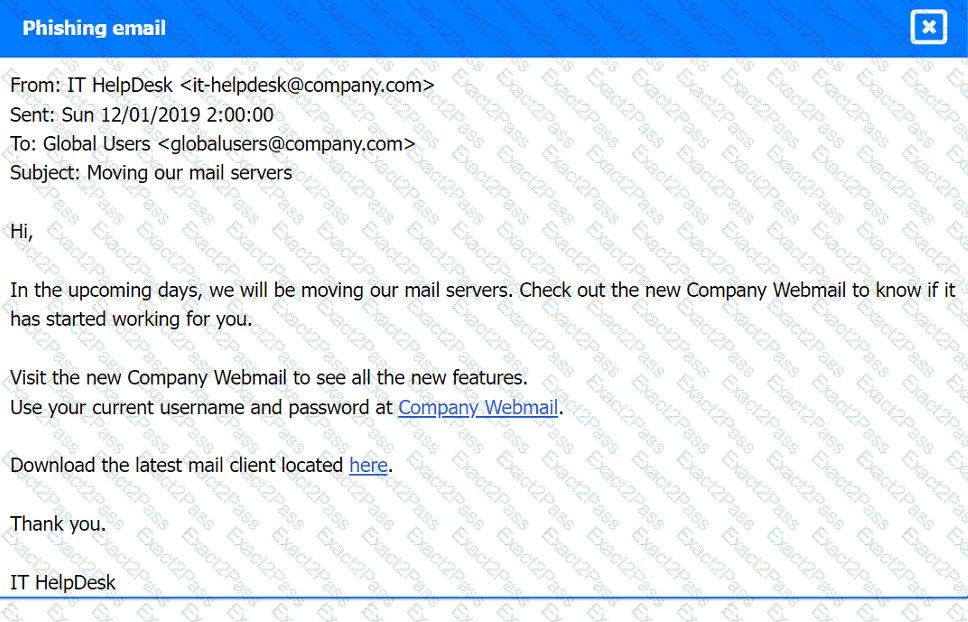
A company recently experienced a security incident. The security team has determined
a user clicked on a link embedded in a phishing email that was sent to the entire company. The link resulted in a malware download, which was subsequently installed and run.
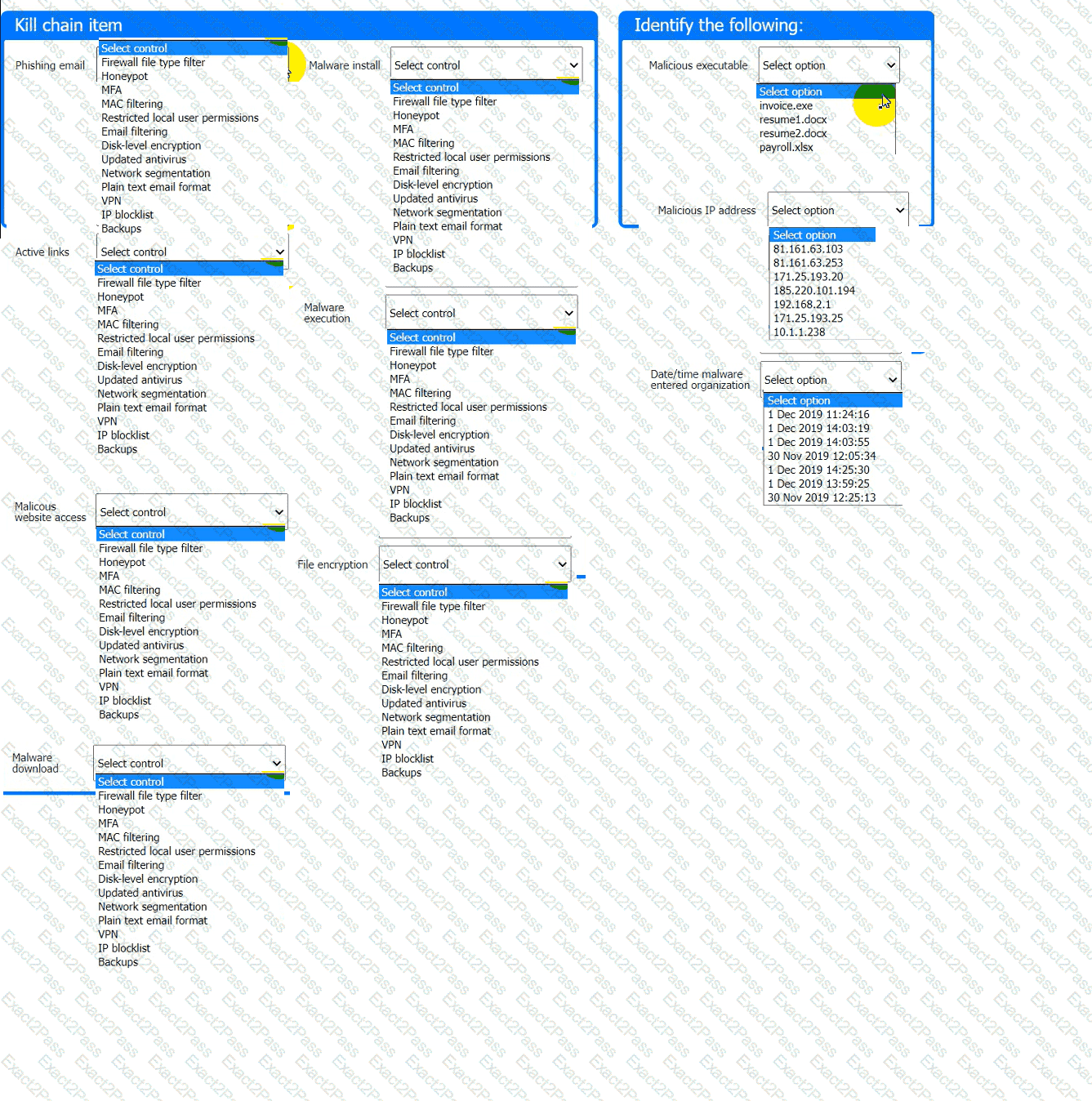
INSTRUCTIONS
Part 1
Review the artifacts associated with the security incident. Identify the name of the malware, the malicious IP address, and the date and time when the malware executable entered the organization.
Part 2
Review the kill chain items and select an appropriate control for each that would improve the security posture of the organization and would have helped to prevent this incident from occurring. Each
control may only be used once, and not all controls will be used.
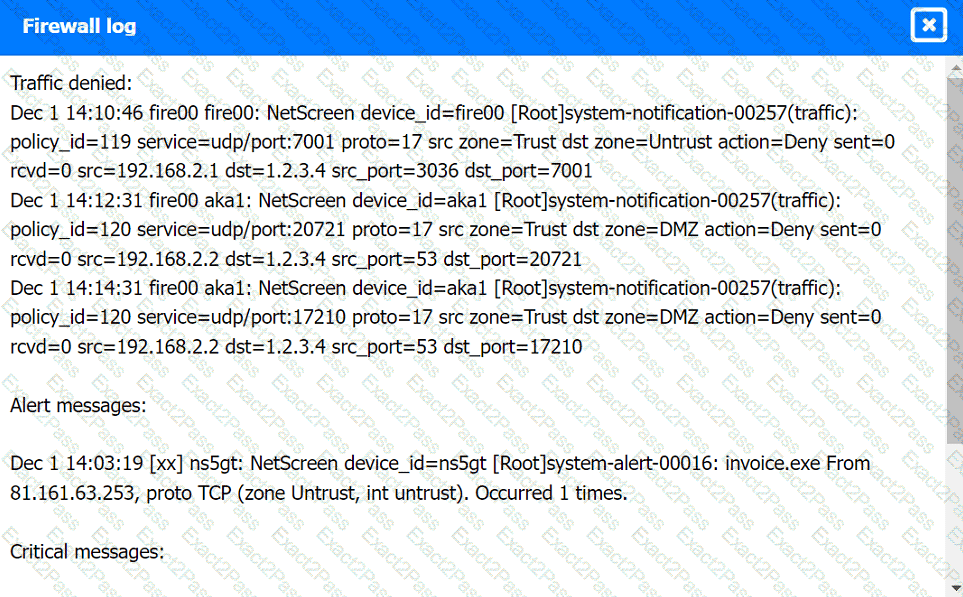
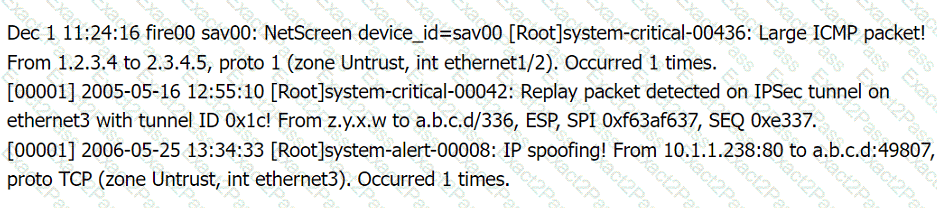
Firewall log:
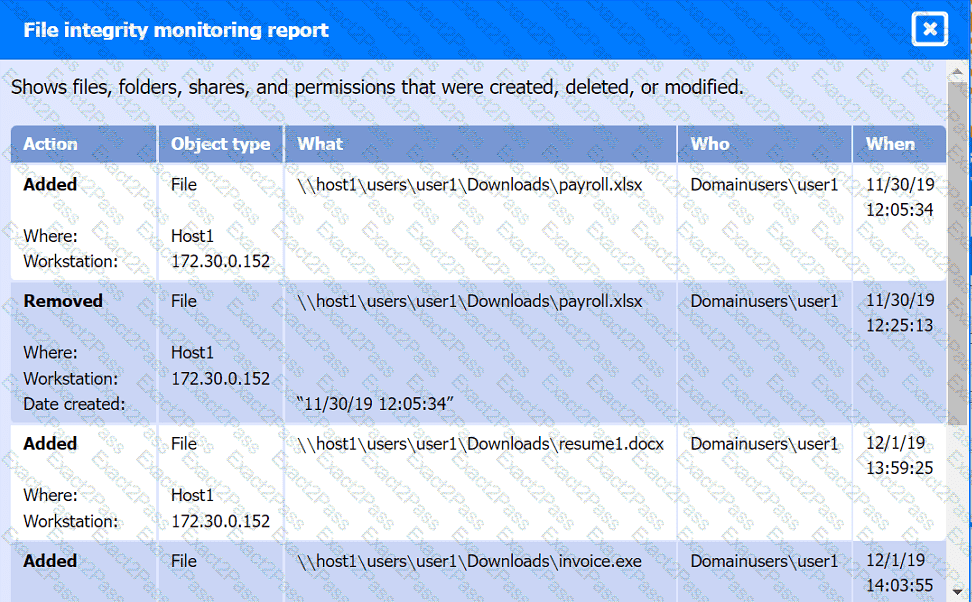
File integrity Monitoring Report:
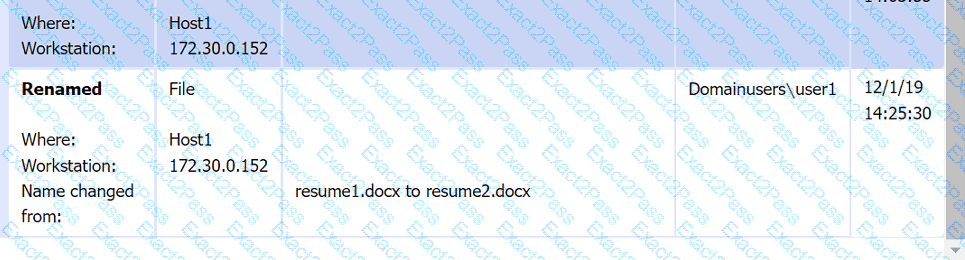
Malware domain list:
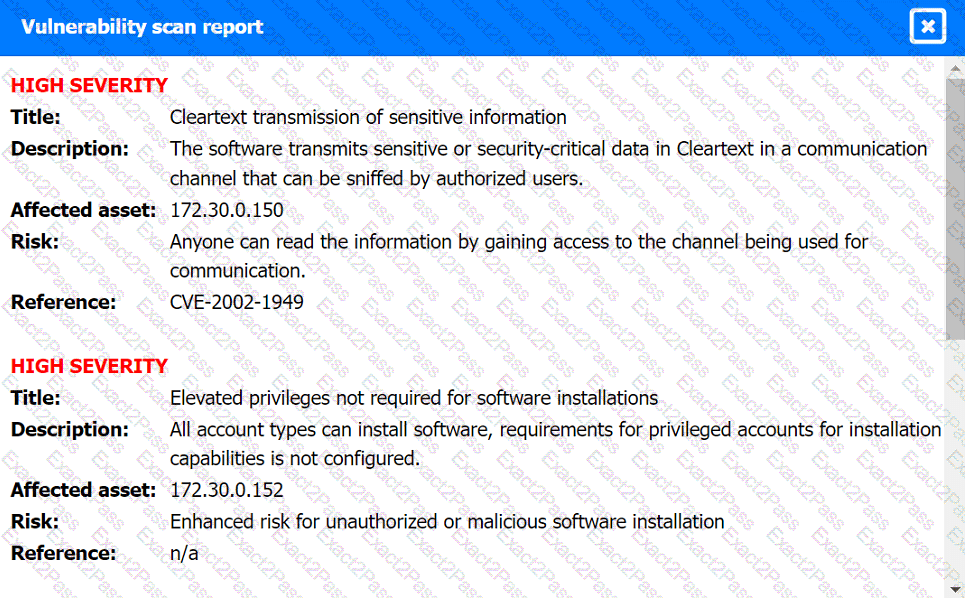
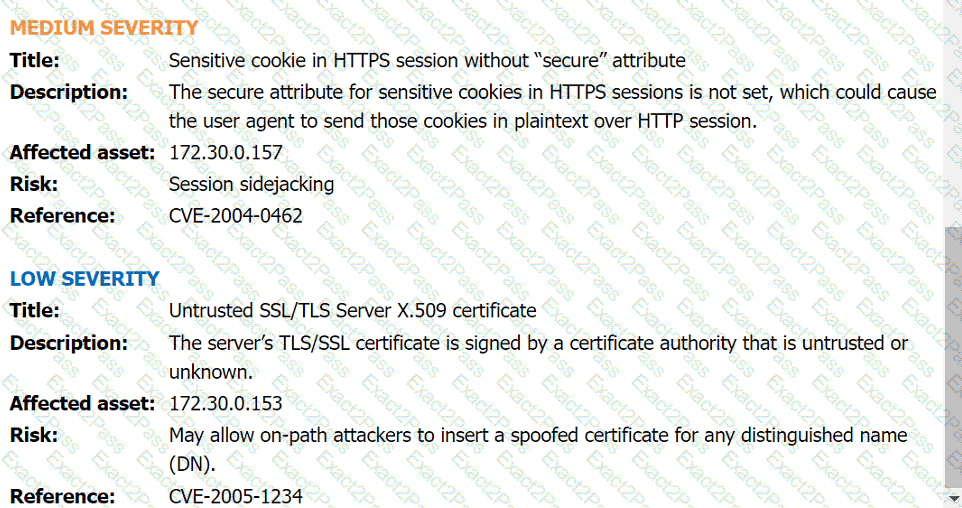
Vulnerability Scan Report:
Phishing Email: