Last Update 7 hours ago Total Questions : 726
The Implementing and Operating Cisco Security Core Technologies (SCOR 350-701) content is now fully updated, with all current exam questions added 7 hours ago. Deciding to include 350-701 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 350-701 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 350-701 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Implementing and Operating Cisco Security Core Technologies (SCOR 350-701) practice test comfortably within the allotted time.
An engineer wants to automatically assign endpoints that have a specific OUI into a new endpoint group. Which
probe must be enabled for this type of profiling to work?
While using Cisco Secure Firewall ' s Security Intelligence policies, which two criteria is blocking based upon? (Choose two.)
How is ICMP used an exfiltration technique?
Which two probes are configured to gather attributes of connected endpoints using Cisco Identity Services
Engine? (Choose two)
A mall provides security services to customers with a shared appliance. The mall wants separation of
management on the shared appliance. Which ASA deployment mode meets these needs?
An engineer configured a new network identity in Cisco Umbrella but must verify that traffic is being routed
through the Cisco Umbrella network. Which action tests the routing?
Why is it important for the organization to have an endpoint patching strategy?
When wired 802.1X authentication is implemented, which two components are required? (Choose two)
What is a benefit of using Cisco AVC (Application Visibility and Control) for application control?
Which feature is used in a push model to allow for session identification, host reauthentication, and session termination?
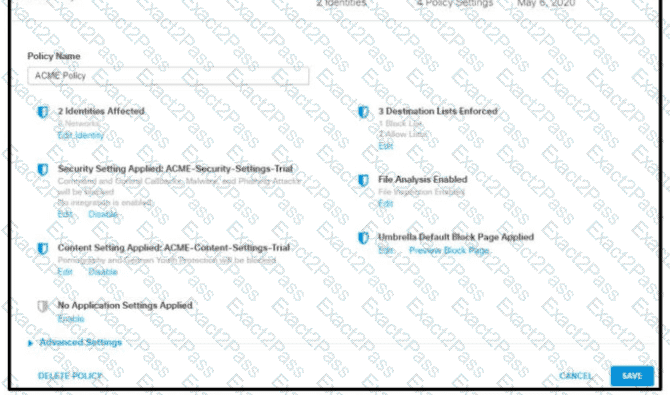
Refer to the exhibit.
How does Cisco Umbrella manage traffic that is directed toward risky domains?
What are two Trojan malware attacks? (Choose two)

